BLUF: Why the United States’ research, intelligence, and national security ecosystem now depends on trusted enabling technologies, resilient supply chains, and controlled delivery
The United States’ most critical federal missions do not fail only because of bad strategy or weak leadership. They fail when the enabling technologies beneath them cannot be trusted. Research, intelligence, defense, health, and other high-consequence operations now depend on semiconductors, computing, communications, software, cyber resilience, and on tightly integrated infrastructure that works exactly as intended. Adversarial nation-states understand this and are targeting the supply chain, the software chain, critical infrastructure, and the trust relationships that hold these systems together. That is why Paragon Micro’s value matters. Through its secure integration facility, discreet handling, controlled validation, and full chain of custody, Paragon Micro helps reduce uncertainty before systems ever reach the mission, turning fragmented delivery into trusted readiness.
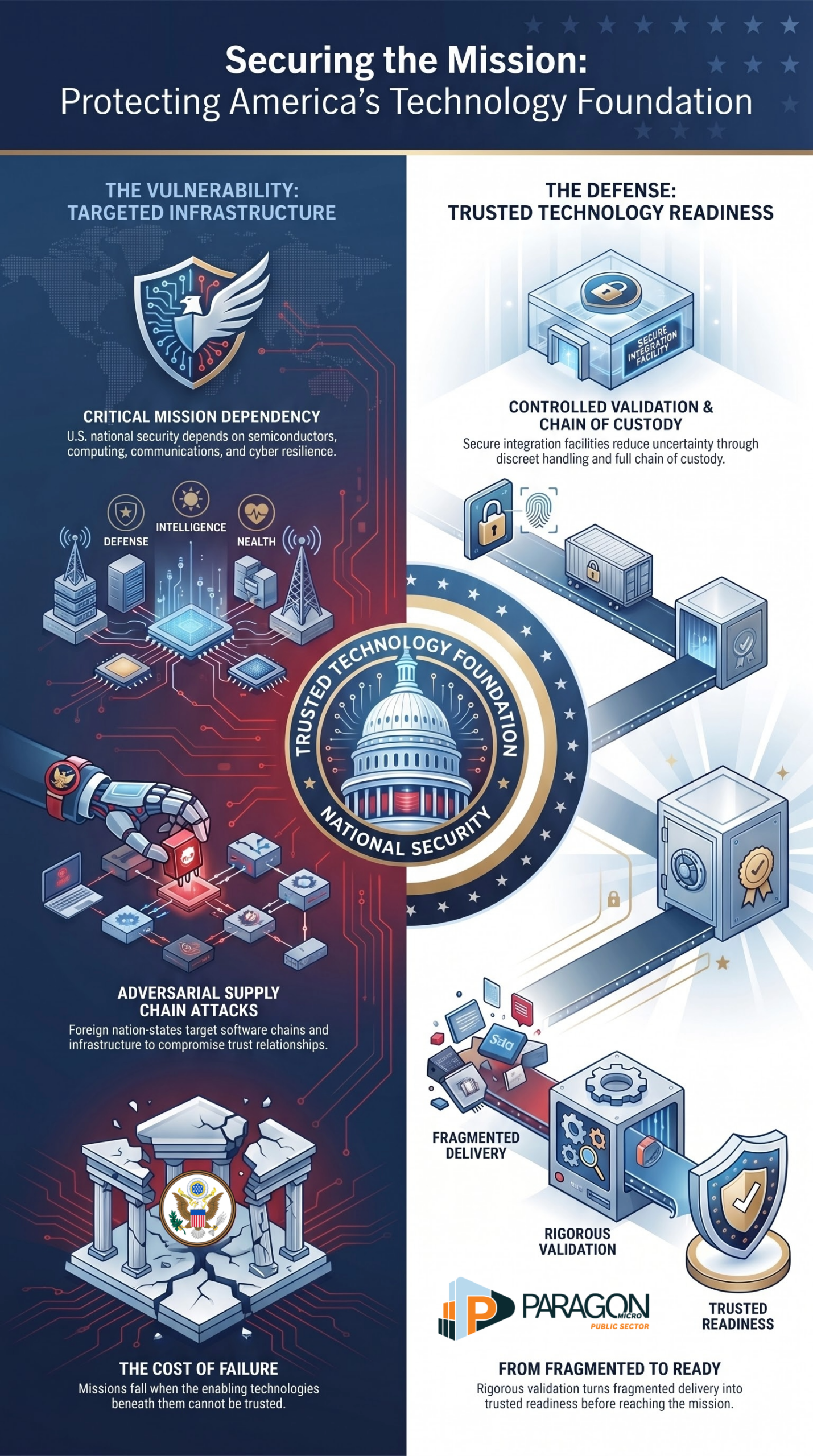
Table of contents
- Chapter 1 | The uncomfortable truth behind modern mission success
- Chapter 2 | The publicly acknowledged federal research and mission ecosystem
- Chapter 3 | The enabling technologies that actually make the mission possible
- Chapter 4 | Compute, storage, and data infrastructure are now strategic assets
- Chapter 5 | Semiconductors decide strategic freedom
- Chapter 6 | Communications, C2, and visibility compress decision time
- Chapter 7 | The edge is unforgiving
- Chapter 8 | Zero trust is not a cyber slogan
- Chapter 9 | Federal health and biomedical missions run on resilient clinical IT
- Chapter 10 | Dependencies and interdependencies are now the battlefield
- Chapter 11 | The nation-state threat is already inside the problem set
- Chapter 12 | Counterfeits, gray market exposure, and lifecycle distortion
- Chapter 13 | Software and firmware are now supply chain terrain
- Chapter 14 | Why fragmented sourcing and field assembly are operationally reckless
- Chapter 15 | How Paragon Micro closes the trust gap
- Summary
- Sources
Chapter 1 — The uncomfortable truth behind modern mission success
The mission now sits on the technology stack
For too long, many leaders have treated technology as support infrastructure rather than mission infrastructure. That mindset is now dangerous. In the federal space, the mission does not sit above the technology stack. It sits on it. Every breakthrough in research, every intelligence assessment, every operational decision, every patient record, every secure collaboration session, every remote field update, and every command-level action now depends on a chain of interconnected systems working exactly as intended. If that chain is weak, delayed, compromised, or poorly understood, the mission absorbs the impact immediately.
Enabling technologies are no longer background tools
This is the uncomfortable truth most organizations still resist. The modern mission is no longer powered only by people, doctrine, and physical infrastructure. It is powered by compute, storage, semiconductors, identity systems, cloud architecture, cyber defenses, visualization platforms, communications, sensors, software, ruggedized endpoints, and resilient networks. These are not background tools. They are mission enablers. They are the conditions that enable execution.
Technology failure is now mission failure
That matters because many senior decision-makers still view technology failures as an IT problem. It is not. In a high-consequence environment, technology failure can lead to mission delay, degraded awareness, broken coordination, corrupted data, denied access, impaired resilience, and, in some cases, operational failure. The system that goes down is rarely just a system. It is usually tied to a larger chain of dependencies that leaders only notice when it breaks.
Mission environments depend on stable digital foundations
A laboratory cannot produce high-value output if its computing environment is unstable. An intelligence organization cannot move at speed if its analysts are working across fragmented tools, incomplete data access, or compromised communications paths. A federal health system cannot maintain continuity if its clinical platforms, infrastructure, storage, and cybersecurity are brittle. A command environment cannot maintain tempo if visual systems, network pathways, edge devices, and decision-support tools fail under pressure. In every one of these examples, the technology is not directly aligned with the mission. It is embedded inside the mission.
The first strategic mistake is ignoring the enabling stack
This is where many organizations make their first strategic mistake. They focus on the visible endpoint and ignore the enabling stack beneath it. They celebrate the application and neglect the infrastructure. They fund the visible capability and underweight the sourcing, integration, validation, and delivery path required to make that capability trustworthy. They assume that if a product is purchased, the problem is solved. It is not solved. It has only entered a more dangerous phase, where hidden weaknesses can be introduced through poor sourcing, weak handling, bad configuration, counterfeit parts, gray-market substitutions, firmware uncertainty, software exposure, or fragmented custody.
National security priorities already reflect this reality
The federal government’s own posture makes this clear. Critical and emerging technologies are not discussed as nice-to-have innovation areas. They are identified as central to national security. That should change how leaders think. The issue is no longer whether advanced computing, networking, microelectronics, cyber resilience, and data infrastructure matter. The issue is whether the organization truly understands how dependent it has become on them, and whether it has taken the operational steps necessary to secure that dependence.
Dependence becomes dangerous when it is unmanaged
Dependence is not weakness by itself. Every advanced mission depends on enabling systems. The real danger comes from unmanaged dependence. That is where interdependencies begin to multiply quietly. A secure endpoint still depends on trusted silicon. Trusted silicon still depends on supply chain integrity. A resilient application still depends on a clean configuration and validated deployment. Identity protection still depends on network architecture, device posture, and access control discipline. Data availability still depends on storage resilience, recovery planning, encryption, and physical protection. Nothing exists alone. Each layer supports another. Each layer can also undermine another when trust breaks.
Supply chain integrity is now part of mission assurance
This is why the old separation between operations, security, logistics, and technology is collapsing. Supply chain integrity is now a mission issue. Configuration control is now a mission issue. Chain of custody is now a mission issue. Field readiness is now a mission issue. The technology lifecycle, from intake through integration to delivery, has become part of mission assurance whether leadership acknowledges it or not.
Risk begins long before deployment
The most dangerous misconception is believing that risk begins once equipment is deployed. In reality, risk begins much earlier. It begins when components are sourced without enough visibility. It begins when products move through too many uncontrolled hands. It begins when validation is assumed instead of documented. It begins when teams trust packaging labels more than provenance. It begins when integration is rushed, staging is fragmented, and accountability is diffused across too many vendors. By the time the system arrives in the field, the most important trust decisions may already be behind it.
Readiness must be redefined
That is why mission success now requires a broader definition of readiness. Readiness is not simply whether a system powers on. Readiness is whether the system is authentic, configured correctly, validated, documented, securely handled, interoperable with adjacent systems, protected during transit, and delivered with accountability. Readiness is whether decision makers can trust what they are receiving before they stake mission performance on it.
Adversaries exploit weak trust relationships
This is also why organizations that still think in narrow procurement terms are falling behind the threat environment. Adversarial states do not care whether your vulnerability was introduced through hardware, firmware, software, transportation, third-party handling, poor lifecycle control, or weak validation. They care that a weakness exists. They care that interdependencies can be exploited. They care that operational trust can be degraded without being immediately detected. The attack surface now includes not only the network but also the supply chain, integration workflow, staging environment, and delivery path.
Clarity must come before confidence
So the first chapter of this discussion is not about fear. It is about clarity. The mission no longer begins at the user interface or at field deployment. It begins much earlier, inside the systems, dependencies, and trust relationships that make the mission executable. Leaders who understand this will design for assurance before deployment. Leaders who ignore it will keep discovering risk too late, after the technology is already in motion and the cost of correction is much higher.
The bottom line
That is the uncomfortable truth behind modern mission success. The mission is only as strong as the enabling technologies beneath it and the discipline used to secure them. Everything else is wishful thinking.
Chapter 2 | The publicly acknowledged federal research and mission ecosystem
The federal mission ecosystem is bigger than most people realize
The United States operates a vast, interconnected research and mission ecosystem that supports national security, intelligence, scientific discovery, public health, energy resilience, and advanced technology development. This system is not limited to a single department or laboratory class. It spans defense research offices, intelligence-focused innovation entities, national laboratories, federally funded research and development centers, civilian agency research hubs, and mission-specific testing and integration environments. Together, these organizations form the publicly acknowledged backbone of federal innovation and mission support.
These institutions do not exist in isolation
One of the biggest mistakes people make is viewing federal research organizations as separate islands. They are not. They operate within a larger national architecture in which agencies define problems, fund priorities, coordinate programs, and depend on a network of performers across government, academia, industry, and specialized research centers. A breakthrough in one part of the ecosystem often depends on infrastructure, expertise, components, data, or testing environments from another. This is not a loose federation. It is a deeply interdependent mission network.
DARPA reflects the model of distributed innovation
DARPA is one of the clearest examples of how this ecosystem works. DARPA is widely known as a defense innovation engine, but it does not operate as a traditional laboratory. Instead, it drives outcomes through program management, technical direction, and a broad network of research performers. That model matters because it shows that federal mission execution often depends less on one physical site and more on the ability to orchestrate highly specialized capabilities across multiple entities. The lesson is important. Mission advantage often comes from coordination as much as invention.
Intelligence missions depend on advanced research
The intelligence community also relies on advanced research structures designed to solve hard, high-consequence problems. Publicly acknowledged organizations such as IARPA help drive innovation for intelligence-related missions by focusing on research with the potential for outsized strategic payoff. This reinforces a central truth. Intelligence advantage is not sustained only by analysts and operators. It is sustained by enabling technologies, data science, computing power, sensing capabilities, communications, and secure systems that underpin them.
The National Laboratories are part of America’s strategic depth
The Department of Energy’s National Laboratories represent another critical layer of the federal public research ecosystem. These laboratories provide unique scientific capabilities, technical infrastructure, and advanced engineering environments that support national priorities spanning energy security, high-performance computing, and national defense-related science. Their role is not symbolic. They provide real capacity, real scale, and real technical depth that the nation depends on for long-term advantage.
FFRDCs expand agency capability where mission demands it
Federally Funded Research and Development Centers exist because agencies need sustained access to highly specialized expertise that cannot always be built organically inside the government. These centers provide continuity, technical focus, and mission alignment in areas where the federal government requires deeper research and development support. They are not generic contractors in the ordinary sense. They are part of the strategic research fabric that helps agencies solve difficult problems across defense, aerospace, energy, public safety, and national security.
Civilian agencies rely on advanced research and technical infrastructure too
This ecosystem is not limited to defense and intelligence. Civilian agencies depend heavily on advanced research, secure infrastructure, high performance computing, specialized networks, resilient storage, analytical environments, and interoperable platforms. Public health, science, environmental monitoring, judicial support, citizen services, transportation, and other civilian missions are increasingly tied to digital and technical capability. The gap between civilian and national security technology dependence is narrower than many assume. Different missions may sound different, but their enabling requirements often look remarkably similar.
Mission execution now depends on shared technological foundations
Across the federal enterprise, the same foundational technology themes keep appearing. Secure compute. Trusted communications. High availability networks. Data platforms. Identity and access control. Specialized endpoints. Visualization systems. Ruggedized field technologies. Storage resilience. Advanced sensing. These are not side capabilities. They are common enablers across a wide range of federal mission environments. The deeper you look, the more obvious the pattern becomes. Different agencies may pursue different outcomes, but many depend on the same classes of enabling technologies to achieve them.
The ecosystem is public, but the stakes are not casual
Even when organizations, labs, and research sponsors are publicly acknowledged, the importance of what they support should not be underestimated. Their missions often align closely with the nation’s most important strategic interests, whether in defense, energy, health, intelligence, or scientific advantage. That means the technology environments that support them cannot be treated casually. Public visibility does not reduce mission sensitivity. In many cases, it increases the importance of getting systems, sourcing, handling, and delivery right.
Complexity is now a defining feature of federal innovation
This ecosystem is powerful but complex. Agencies do not simply buy technology and move on. They depend on layered relationships between sponsors, program offices, labs, integrators, OEMs, software providers, logistics workflows, security requirements, and mission owners. That complexity creates both capability and vulnerability. It enables specialization, but it also creates more dependency chains, more integration points, and more places where trust can break down if not managed carefully.
Interdependence is what makes the ecosystem strong and fragile
The very thing that gives the federal research and mission ecosystem its strength also exposes it. These organizations are linked through shared infrastructure, suppliers, technology categories, and a shared dependence on trusted delivery. A weak point in one layer can ripple outward. A supply chain issue affecting microelectronics, for example, can impact research timelines, operational readiness, and modernization efforts across multiple agencies at once. The ecosystem is strong because it is connected. It is fragile for the exact same reason.
This is why enabling technology matters so much
Understanding the ecosystem is only the first step. The real point is that these agencies and institutions do not achieve mission outcomes through policy language alone. They depend on technology environments that must be secure, resilient, interoperable, and trusted. Their success depends on whether the systems underlying the mission are authentic, available, correctly configured, and protected from compromise before they enter operational use. That is where the conversation moves from organizational structure to enabling technology.
The bottom line
The publicly acknowledged federal research and mission ecosystem is not a loose collection of agencies and laboratories. It is a national capability network built on interdependence, specialization, and enabling technology. The more critical the mission, the more important those underlying systems become. To understand how these agencies accomplish their work, you have to understand the infrastructure, technologies, and trust relationships that make that work possible in the first place.
Chapter 3 | The enabling technologies that actually make the mission possible
The mission depends on more than talent and intent
Every federal mission sounds different on paper. Some focus on defense. Some support intelligence. Some advanced science, health, energy, or public service. Yet beneath those mission sets sits a common reality. None of them operates on strategy alone. None of them succeed on leadership talking points. None of them scale on institutional reputation. They run on enabling technologies that make execution possible, repeatable, secure, and resilient.
That is the layer that too many organizations still underestimate. They talk about outcomes, but not the systems required to produce them. They talk about transformation, but not the infrastructure that carries the load. They talk about readiness, but not the technology stack that determines whether readiness is real or just assumed.
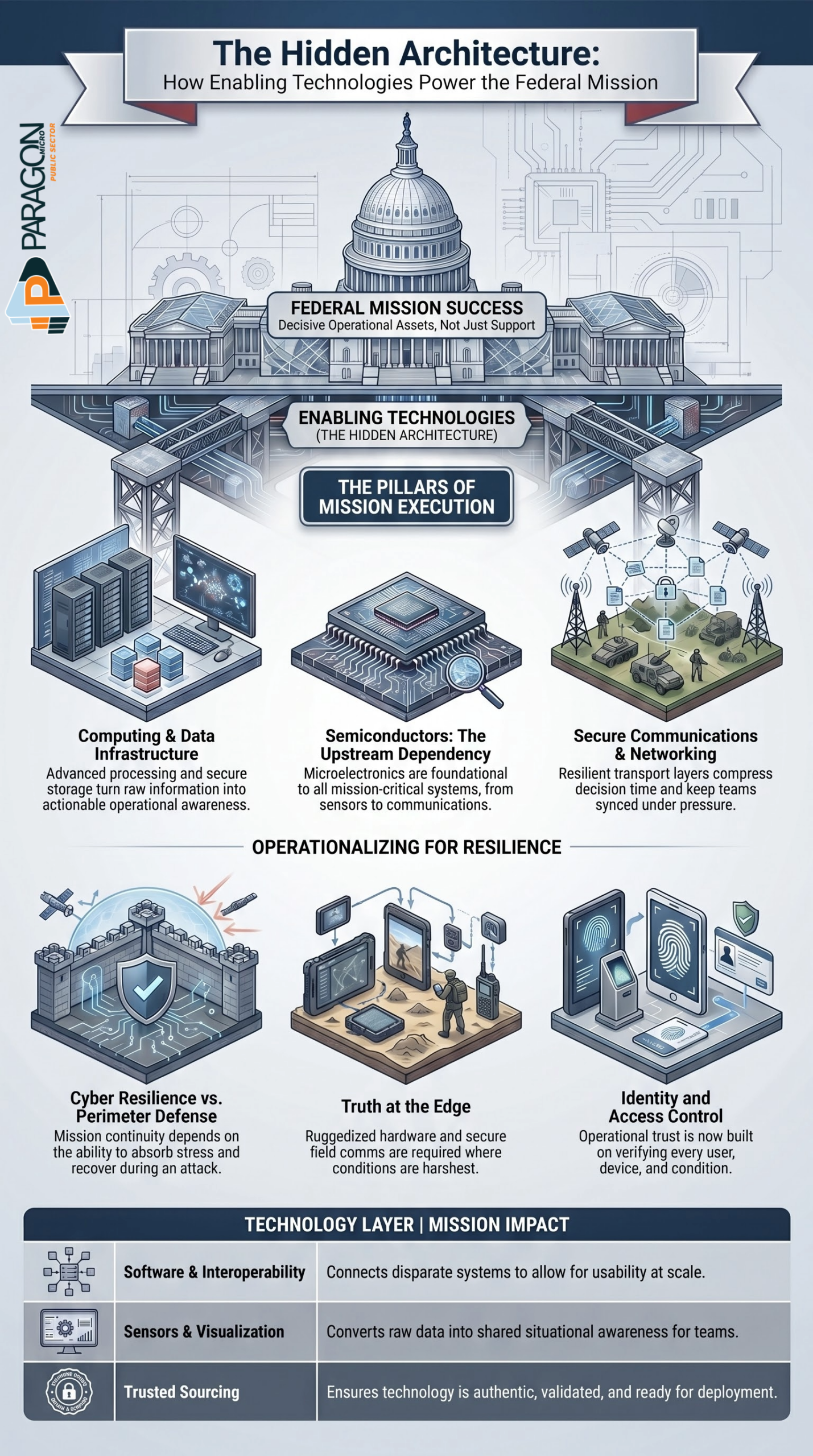
Enabling technologies are the hidden architecture of execution
Enabling technologies are the systems, platforms, components, and digital foundations that enable agencies to operate in real-world conditions. They are not always the most visible part of the mission, but they are often the most decisive. They include advanced computing, secure storage, semiconductors, communications networks, cyber defenses, identity systems, software platforms, rugged devices, sensors, visualization tools, cloud environments, and resilient edge infrastructure.
These technologies are often treated as supporting assets. That is the wrong frame. They are operational assets. They shape speed, trust, access, survivability, coordination, and mission continuity. Without them, the mission does not merely slow down. It begins to degrade.
Advanced computing has become a mission requirement
Modern federal operations depend on the ability to process, analyze, model, store, and move large volumes of data at speed. Whether the mission involves intelligence analysis, scientific simulation, logistics coordination, patient support, or operational planning, advanced computing now sits at the center of performance.
This includes high-performance computing environments, distributed processing, edge computing, storage architecture, cloud infrastructure, and AI-ready platforms. When computing capacity is weak, organizations do not simply lose efficiency. They lose analytical depth, decision speed, modeling capability, and operational responsiveness. In a high-consequence environment, that delay carries a strategic cost.
Data infrastructure determines whether information becomes action
Data is only useful when it can be trusted, accessed, secured, shared appropriately, and processed in time to matter. That means the real issue is not whether an agency has data. The real issue is whether it has the infrastructure to operationalize data.
Data platforms, secure storage, interoperability layers, backup and recovery design, access controls, and network availability all determine whether information becomes awareness or noise. A mission environment flooded with data but weakened by fragmentation, latency, poor structure, or weak access governance is not empowered. It is burdened.
Semiconductors are upstream from almost everything
Few technologies are more foundational than semiconductors. They sit inside computer systems, communications equipment, sensors, control platforms, rugged devices, storage systems, and countless other mission-critical technologies. That is why semiconductor access, provenance, resilience, and trust matter far beyond manufacturing policy.
When semiconductor risk enters the system, it ripples outward. Procurement timelines become unstable. Trusted availability becomes uncertain. Modernization slows. Strategic dependence deepens. This is why microelectronics are not a niche concern. They are foundational dependencies that shape the reliability of the broader mission stack.
Communications and networking technologies compress decision time
Secure and resilient communications are what connect the mission to itself. They allow people, systems, data, and command elements to move in sync rather than in fragments. Networking infrastructure, wireless technologies, satellite communications, software-defined systems, and secure transport layers all play a role in whether an organization can coordinate under pressure.
This is especially important in environments where delays can change outcomes. Decision quality depends on visibility. Visibility depends on data flow. Data flow depends on the integrity and resilience of the communications path. When networks degrade, trust degrades with them. Teams stop sharing a common picture. Coordination begins to fracture. Tempo drops.
Identity and access control now shape operational trust
One of the biggest shifts in modern mission design is the growing importance of identity, authentication, authorization, and device trust. In the past, organizations often relied on network boundaries and implicit trust models. That era is over. Today, who is accessing what, from where, with what device, under what conditions, matters more than ever.
Identity systems, privileged access controls, device posture checks, and segmented access models now shape whether organizations can protect sensitive data, sustain collaboration, and contain compromise without paralyzing operations. Access is no longer a simple IT issue. It is part of mission assurance.
Cyber resilience is now inseparable from mission continuity
It is no longer enough to defend systems only against intrusion. Agencies must also ensure they can continue operating when an attack, disruption, or compromise occurs. That is why cyber resilience matters. It extends beyond perimeter security and into recovery, segmentation, redundancy, secure architecture, and continuity of operations.
In practical terms, cyber resilience is what determines whether an incident becomes a contained disruption or a cascading failure. A fragile environment can look functional during normal conditions and still collapse under real pressure. A resilient environment is built to absorb stress, preserve critical operations, and recover with discipline.
The edge introduces a harsher standard of truth
Mission success does not always happen in controlled enterprise environments. Many federal operations depend on technology at the edge, where conditions are less forgiving, and support is limited. This includes mobile teams, harsh environments, disconnected operations, tactical deployments, temporary sites, and remote field locations.
At the edge, equipment must do more than work in theory. It must survive real conditions. Power constraints, degraded communications, environmental stress, limited maintenance windows, and physical exposure all raise the standard. Rugged compute, resilient networking, secure field communications, portable power, and deployable infrastructure become essential because failure at the edge is often immediate and visible.
Sensors and visualization systems shape situational awareness
Many mission environments rely on sensing technologies, visualization systems, dashboards, command displays, monitoring tools, and decision support platforms to convert raw information into shared awareness. These technologies are often overlooked because they sit at the intersection of hardware, software, network infrastructure, and user workflow.
Yet they are central to how teams interpret reality. If sensing is weak, visibility suffers. If visualization is poor, understanding lags. If integration is fragmented, people make decisions based on partial contexts. The mission then suffers not because information did not exist, but because the environment did not present it clearly, securely, or in time.
Software is the connective layer across the stack
Hardware may carry the mission, but software increasingly directs it. Operating systems, orchestration layers, analytics tools, firmware, collaboration platforms, automation logic, and management interfaces connect the broader environment together. That means software risk is not confined to one application. It can affect performance, trust, security, interoperability, and lifecycle control across multiple layers at once.
This is why software assurance matters so much. The environment is only as trustworthy as the code, configurations, updates, integrations, and dependencies that shape its behavior. Poor software discipline can quietly undermine otherwise strong infrastructure.
Interoperability is what makes technology useful at scale
Federal mission environments rarely rely on a single platform, vendor, or architecture. They depend on mixed environments, legacy platforms, modernized systems, shared data flows, specialized tools, and cross-functional coordination. That means interoperability is not optional. It is what allows technology to become usable at scale.
The system that works on its own but fails to integrate cleanly with adjacent systems is not a strategic asset. It is friction. Real mission value comes from technologies that can coexist, exchange data, support workflow, and align to operational reality without introducing unnecessary burden.
These technologies are interdependent by design
The most important truth in this chapter is that none of these technologies stands alone. Computing depends on trusted chips. Data depends on storage and access control. Communications depend on secure infrastructure. Visualization depends on data flow. Edge systems depend on rugged hardware, resilient power, and software integrity. Identity depends on policy, architecture, and enforcement. Cyber resilience depends on all of it working together.
That is why the conversation cannot stop at capabilities. It must include dependencies and interdependencies. A weakness in one enabling layer can compromise confidence in another. A break in the chain can ripple across the mission faster than leadership expects.
Agencies do not just need technology; they need trusted technology
This is the real distinction. Federal agencies do not simply need advanced systems. They need systems they can trust. Trust means the technology is authentic. It means it has been properly sourced, handled carefully, configured correctly, thoroughly validated, documented clearly, and delivered with accountability. It means the organization knows what it is deploying, how it was prepared, and whether it is truly ready.
That is where many modernization efforts stumble. They focus on acquiring capability but fail to secure the trust conditions that support it. In today’s threat environment, that gap is dangerous.
The bottom line
The mission is accomplished through enabling technologies, whether leaders choose to acknowledge it or not. Advanced computing, data infrastructure, semiconductors, communications, cyber resilience, identity systems, software, edge platforms, and interoperable architectures now form the hidden architecture of federal execution. These are not secondary tools. They are the conditions that enable mission performance. The agencies that understand this will build around trust, resilience, and controlled delivery. The ones that do not will keep mistaking acquisition for assurance.
Chapter 4 | Compute, storage, and data infrastructure are now strategic assets
The mission runs on a digital backbone
Compute, storage, and data infrastructure are no longer back-office utilities. They are now part of the mission itself. Research environments need processing power. Intelligence functions need fast access to trusted data. Federal health systems need resilient clinical platforms. Command environments need secure, real-time information flow. If the digital backbone is weak, the mission slows down with it.
Data is only valuable if it is usable
Many organizations treat data as an asset by default. It is not. Data only becomes useful when it can be stored securely, accessed quickly, processed reliably, and shared appropriately. Without the right infrastructure, data becomes fragmented, delayed, or unusable at the moment it is needed most.
Storage and compute shape decision speed
The ability to move from information to action depends on more than software. It depends on the infrastructure underneath it. Processing capacity, storage resilience, backup design, network access, and system availability all shape whether leaders can make decisions with confidence or whether teams are stuck waiting on systems that cannot keep up.
Fragile infrastructure creates hidden mission risk
Weak compute environments do not always fail loudly at first. Sometimes they fail due to latency, bottlenecks, limited scalability, inconsistent access, or recovery gaps. That kind of weakness is dangerous because it quietly erodes performance before leadership sees the full impact. By the time the breakdown is obvious, the mission may already be behind.
Strategic infrastructure must be trusted infrastructure
This is why compute and data infrastructure cannot be treated like ordinary commodity purchases. Agencies need more than equipment. They need systems that are properly sourced, securely integrated, validated before deployment, and delivered with accountability. Strategic infrastructure only becomes a strategic advantage when it is trusted.
The bottom line
Compute, storage, and data infrastructure now determine how fast, securely, and reliably federal missions can operate. They are not background support systems. They are strategic assets that shape execution, resilience, and mission confidence.
Chapter 5 | Semiconductors decide strategic freedom
Chips sit beneath almost every mission system
Semiconductors are easy to ignore because most people never see them. Yet they sit at the heart of nearly every mission-critical system the federal government depends on. Compute platforms, communications gear, sensors, storage systems, cyber tools, medical devices, industrial controls, and rugged field equipment all rely on microelectronics to function.
A chip shortage is never just a manufacturing problem
When semiconductor access is disrupted, the impact spreads fast. Procurement slows. Modernization timelines slip. Maintenance gets harder. Trusted replacements become harder to find. What appears to be a supply issue at the component level quickly becomes an operational issue at the mission level.
Dependence creates strategic exposure
This is what makes semiconductors so important. Agencies are not only dependent on finished systems. They are dependent on the tiny upstream components that make those systems possible. If the source, integrity, or availability of those components is uncertain, the broader mission stack becomes less stable.
Trust matters as much as availability
Getting chips is not enough. Agencies need confidence that the components inside their systems are authentic, uncompromised, and sourced through trusted channels. Counterfeit parts, gray market substitutions, and weak provenance introduce risk long before a system is powered on.
Strategic freedom depends on trusted microelectronics
The ability to execute national security, research, intelligence, and critical infrastructure missions depends in part on whether the United States and its partners can access a trusted semiconductor supply. This is not a niche technical issue. It is a core strategic issue that affects readiness, resilience, and long-term freedom of action.
The bottom line
Semiconductors may be small, but their importance is enormous. They shape whether mission systems can be built, sustained, trusted, and delivered on time. In modern federal operations, chips do not just support the mission. They help determine whether the mission can move at all.
Chapter 6 | Communications, C2, and visibility compress decision time
The mission moves at the speed of communication
In high-consequence environments, communication is not a support function. It is what keeps the mission synchronized. Combatant commands, joint task forces, special operations elements, maritime forces, and intelligence supported teams all rely on secure, reliable information flow to maintain awareness and act in time. When communication degrades, the mission does not simply become less efficient. It becomes less coherent.
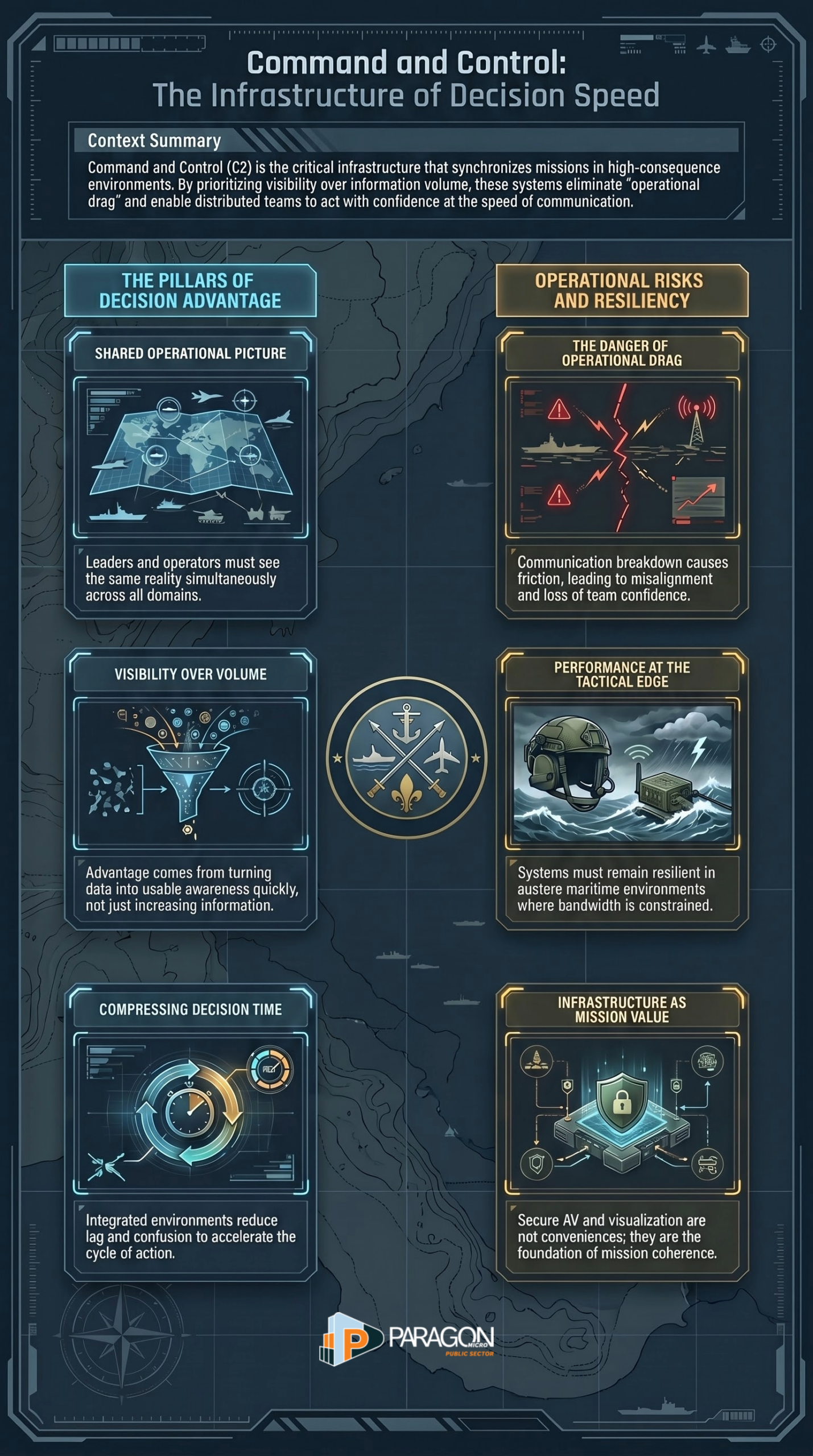
Command and control depends on a shared operational picture
Command and control only works when leaders, operators, and supporting teams can see the same reality at the same time. That applies inside combatant command headquarters, forward operational centers, maritime command nodes, and special mission environments that depend on fast coordination across multiple domains. U.S. Special Operations Forces, Navy SEAL teams, and JSOC-aligned mission sets operate in environments where fragmented visibility can have immediate consequences. They need more than screens and networks. They need integrated environments that support speed, trust, and clarity under pressure.
Decision advantage comes from visibility, not volume
More information does not automatically create better decisions. The real advantage comes from turning information into usable awareness quickly enough to matter. That is why secure AV, visualization, collaboration, and C2 environments matter so much. Leaders need to see the operating picture clearly. Operators need to understand changes as they happen. Distributed teams need to coordinate without losing time to confusion, lag, or incompatible systems. In these environments, visibility is not a convenience. It is a decisive advantage.
Delay creates operational drag
When communications break down or C2 environments lose fidelity, the effects spread fast. Teams start working from partial information. Coordination slows. Confidence drops. Misalignment grows. That kind of friction is dangerous in any federal mission, but it is especially dangerous for combatant commands, maritime operators, special operations teams, and joint mission sets where timing, synchronization, and trust shape outcomes in real time.
Maritime and special operations environments raise the standard
The burden is even higher for forces operating at sea or in austere environments. Ships, expeditionary teams, and special operations units cannot depend on fragile communications paths or poorly integrated systems. Navy SEALs and other special operations elements often operate where bandwidth is constrained, conditions are unstable, and coordination windows are short. In those environments, communications and C2 systems must remain clear, resilient, and interoperable. If they do not, the mission pays for the gap immediately.
This is why we build for operational fidelity
We treat communications, C2, and operational workspaces as mission infrastructure. We design these environments to support real-time collaboration, operational fidelity, secure visualization, and decision support for organizations that cannot afford confusion. That includes headquarters environments, mission coordination spaces, command centers, and other high-consequence settings where every delay carries a cost. We do not view this as ordinary AV. We view it as the infrastructure behind decision speed.
The bottom line
Combatant commands, special operations forces, Navy SEAL teams, JSOC-aligned mission sets, and other high-consequence organizations depend on communications and C2 environments that compress decision time rather than add friction. The mission moves at the speed of trust, visibility, and coordination. When those systems are strong, leaders can act with confidence. When they are weak, even the best teams lose time they cannot afford.
Chapter 7 | The edge is unforgiving
The edge is where theory gets exposed
The edge is where mission systems stop living in controlled environments and start operating under real pressure. It is where heat, salt, vibration, limited bandwidth, intermittent power, long logistics tails, and physical threat converge. In those conditions, technology is not judged by its brochure. It is judged by whether it still works when the environment is actively trying to break it. That is why edge systems matter so much to federal missions. They carry the burden in places where failure is immediate, and recovery is rarely convenient.
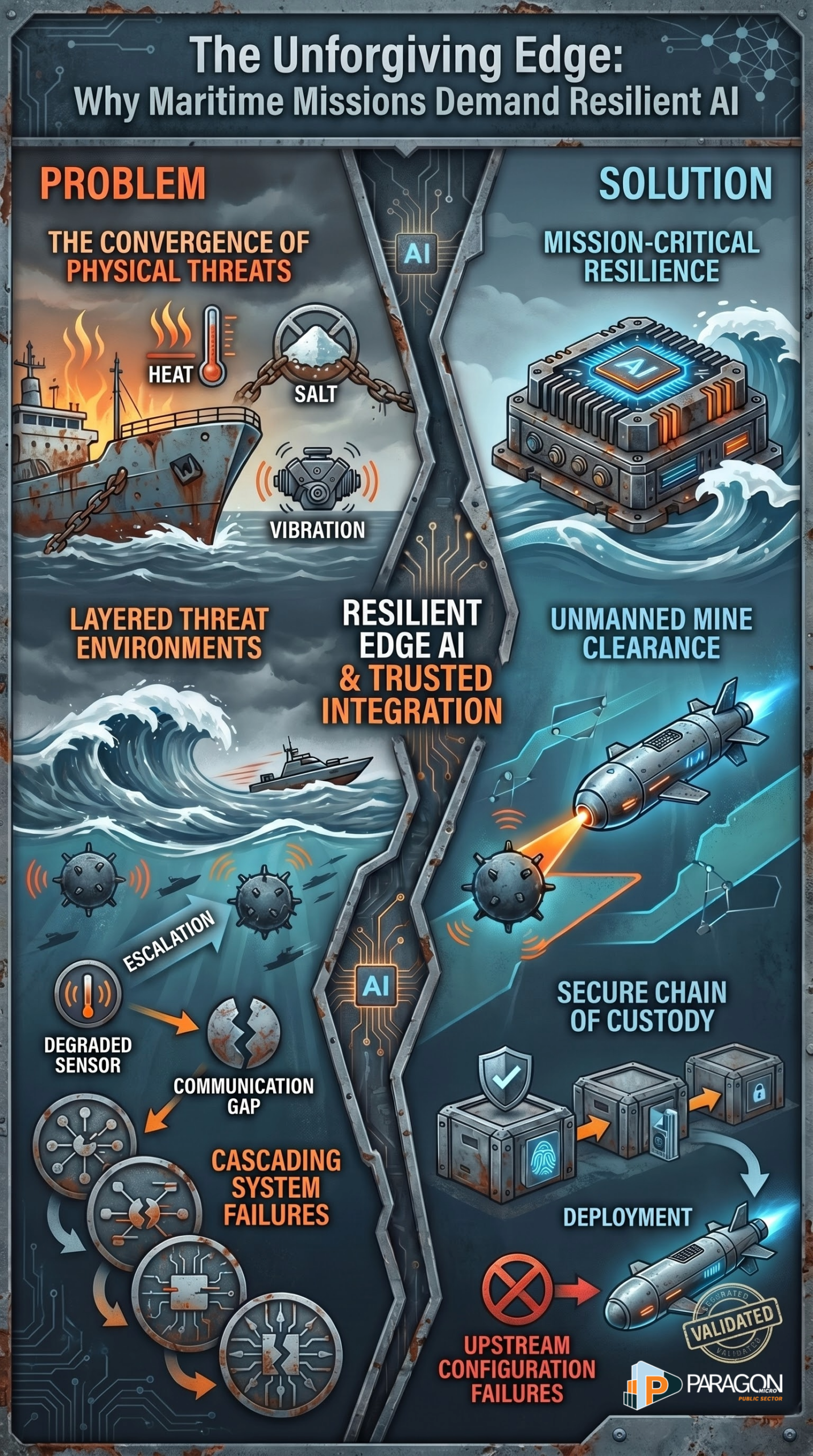
The current maritime fight proves the point
The current Middle East operating environment makes this painfully clear. Reuters reports that after a six-week U.S. conflict with Iran, shipping in and around the Strait of Hormuz has remained heavily disrupted, with vessels stranded, maritime traffic constrained, and naval forces focused on keeping sea lanes usable. Reuters also reports that the U.S. has been conducting mine clearance operations in the Strait of Hormuz using unmanned systems, helicopters, and specialized ships because the environment remains dangerous, complex, and slow to secure. This is not a clean enterprise network problem. This is contested infrastructure under maritime threat.
Ships at sea are now operating inside a layered threat environment
Ships at sea in this environment are not dealing with one threat at a time. Reuters reports risks from sea mines, fast attack craft, disrupted passage, and regional military escalation around the Strait of Hormuz. At the same time, CENTCOM has continued to describe the Houthis’ threat to global maritime activity in and around the Red Sea as serious enough to require ongoing coalition action. In practical terms, maritime operators now face a layered edge environment in which mobility, communications, sensing, survivability, and logistics must work together at once.
Maritime operations demand rugged, resilient systems
This is exactly why ordinary commercial assumptions fail at the edge. A ship at sea cannot depend on fragile equipment, casual integration, or uncertain configuration. It needs systems that can tolerate motion, corrosion, signal degradation, limited repair windows, and prolonged operational stress. Communications have to persist when conditions degrade. Compute has to function when reachback is limited. Sensors have to remain reliable when crews are making decisions with limited time and little margin for error. In maritime operations, the edge does not reward convenience. It rewards resilience.
The Red Sea and Hormuz prove that distance does not reduce risk
One of the biggest misconceptions in technology planning is that risk is greatest only at fixed installations or inside enterprise environments. The Red Sea and Strait of Hormuz prove the opposite. These maritime corridors are among the most important routes in the world, and they are also spaces where ships, crews, logistics chains, and mission systems can be pressured far from shore. The International Maritime Organization describes the Red Sea route from the Suez Canal through Bab el Mandeb to the Gulf of Aden as one of the world’s most critical maritime corridors. When that environment is threatened, it affects shipping, energy movement, operational planning, and allied confidence at the same time.
Mine warfare shows why edge technology matters
Mine clearance is one of the clearest examples of why enabling technologies at the edge are so important. Reuters reports that current U.S. operations in the Strait of Hormuz rely on underwater drones, remotely operated systems, helicopters, divers, and modern mine-hunting tools because clearing mines is slow, dangerous work that demands precision. That tells you something bigger. At sea, advanced technology is not an optional enhancement. It is what allows operators to reduce exposure, extend reach, and preserve mission continuity in environments where human crews remain vulnerable.
Edge failure cascades quickly
When a system fails at sea, the impact rarely stays local. A degraded sensor affects awareness. A communications issue affects coordination. A power or computing problem affects timing. A navigation, identification, or mission system issue can affect the entire vessel’s posture. In contested maritime environments, those failures can spread from inconvenience to operational danger fast. Reuters reporting on shipping disruption, course reversals, blockades, and stranded vessels around Hormuz shows how quickly uncertainty at sea can scale into regional economic and security consequences.
This is why trusted preparation matters before deployment
The lesson for agencies and mission owners is straightforward. Edge systems cannot be treated as simple product deliveries. They must be sourced through trusted channels, configured correctly, tested in controlled environments, validated before fielding, and delivered with accountability. In maritime and other edge missions, the worst time to discover weak integration, questionable provenance, or configuration drift is after the system is already underway. That is where Paragon Micro’s model becomes relevant. A secure facility, controlled integration, discreet handling, and full chain of custody help reduce the risk that systems arrive at the edge already compromised by preventable upstream failures.
The bottom line
The edge is unforgiving because it strips away assumptions. The current war environment in the Middle East, from Red Sea threats to Strait of Hormuz disruption and mine clearance, shows that ships at sea now operate in conditions where ruggedization, trusted communications, resilient compute, secure integration, and disciplined delivery are mission requirements. At the edge, there is no safe distance from consequence. Systems either hold up under pressure, or the mission pays for the gap.
Chapter 8 | Zero trust is not a cyber slogan
The country is being hit by real, active cyber threats now
Zero trust matters because the threat is not hypothetical. CISA continues to add newly exploited flaws to its Known Exploited Vulnerabilities Catalog, including entries added on April 14 and April 16, 2026, based on evidence of active exploitation in the wild. That matters because it shows the U.S. threat environment is not static. It is a rolling stream of attackers finding and using weaknesses faster than many organizations can patch them.
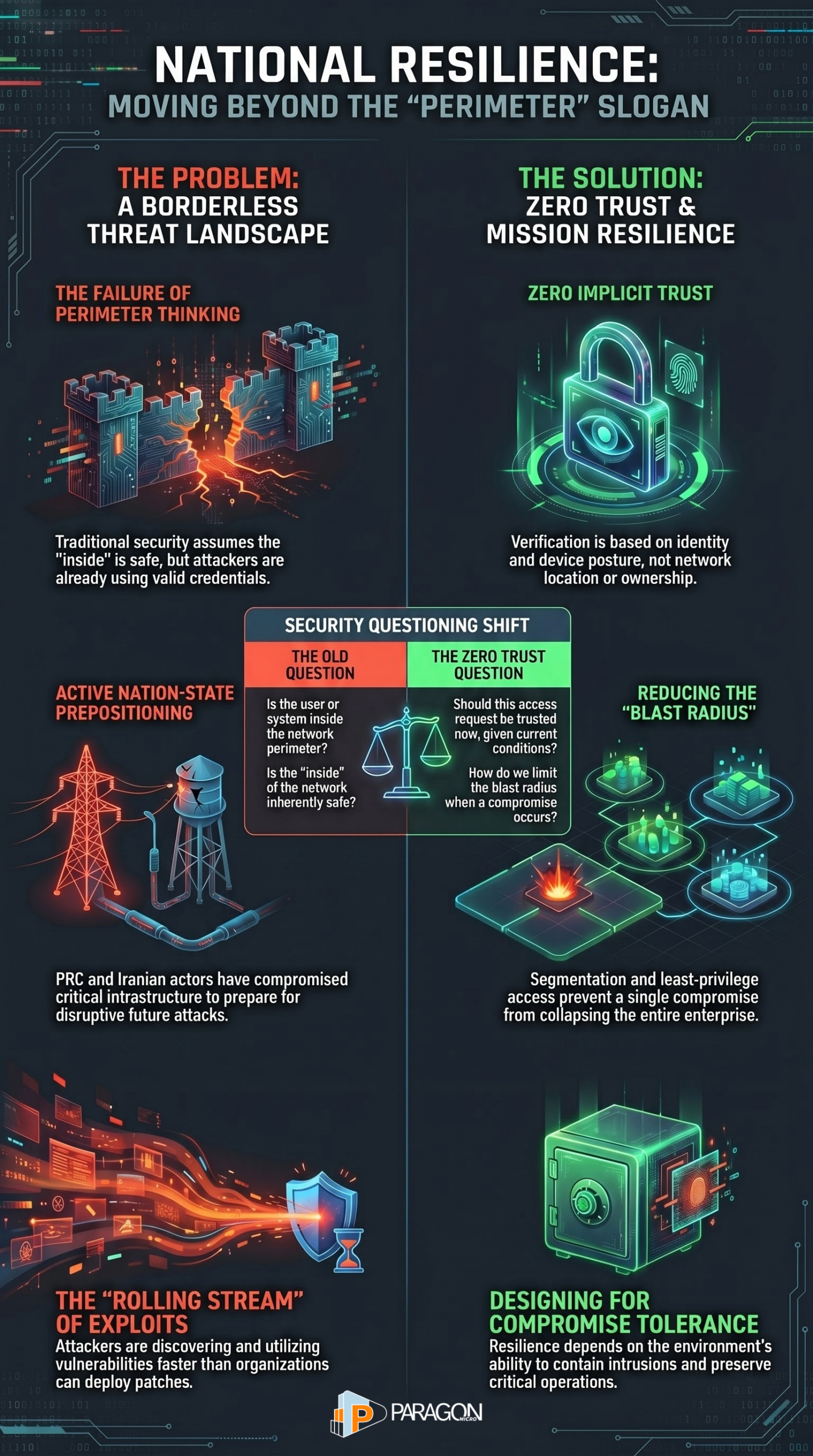
Nation-state actors are targeting critical infrastructure
The broader strategic threat is even more serious. The 2025 Annual Threat Assessment states that China remains the most active and persistent cyber threat to the U.S. government, the private sector, and critical infrastructure networks. CISA’s Volt Typhoon advisory says PRC state-sponsored actors compromised multiple U.S. critical infrastructure organizations and maintained access in part to preposition for disruptive or destructive effects in the event of a major crisis. The FBI has also warned in early 2026 that nation-state actors are targeting American businesses in critical infrastructure directly and through proxies to steal, surveil, and preposition access for later use.
The threat is not limited to one country or one method
The current threat picture is not only about PRC activity. On April 7, 2026, CISA published a joint advisory warning that Iranian-affiliated cyber actors had exploited programmable logic controllers across U.S. critical infrastructure. The Justice Department also announced in March 2026 that it disrupted an Iranian cyber-enabled psychological operations effort directed at dissidents and critics, showing that hostile cyber activity against U.S. interests spans infrastructure targeting, influence operations, intimidation, and hybrid campaigns.
Old perimeter thinking does not match the threat environment
That is why zero trust matters. NIST defines zero trust as an approach that assumes no implicit trust based on network location, asset ownership, or user status. In today’s environment, that is not a trendy framework. It is a realistic response to adversaries who are already inside networks, abusing valid credentials, exploiting exposed systems, and attempting to persist quietly for future leverage. The old model assumed the inside was safer than the outside. Current cyber activity shows that the assumption is no longer credible.
Zero trust changes the question
Instead of asking whether a user or system is inside the perimeter, zero trust asks whether this access request should be trusted now, given current conditions. That means identity, device posture, segmentation, least privilege, logging, validation, and continuous verification all become central. In practical terms, zero trust is about reducing the blast radius when a compromise occurs and preventing a single foothold from becoming enterprise-wide access. That is exactly the kind of operating discipline a country needs when critical infrastructure is being targeted by persistent adversaries.
Mission resilience now depends on compromise tolerance
This also connects directly to mission resilience. Organizations can no longer design only for prevention. They have to design for survival under pressure. If an exploited vulnerability slips through, if a credential is stolen, or if a contractor, remote connection, or field asset becomes the entry point, the environment must be able to contain the intrusion and preserve critical operations. That is the deeper value of zero trust. It is not only about blocking attackers. It is about keeping the compromise from collapsing. This is an inference drawn from the current advisory pattern and the logic of zero-trust architecture.
This is where Paragon Micro becomes relevant
Paragon Micro’s Zero Trust & Cyber Resilience positioning matters in this context because it aligns with the real problem. When critical infrastructure and federal environments are targeted by active exploitation, prepositioning campaigns, and abuse of industrial control systems, agencies need more than security software. They need environments built around trusted identity, controlled access, segmented architecture, resilient infrastructure, and systems that are securely sourced, integrated, and delivered. Zero trust is not a cyber slogan. It is the operating model for a country under sustained digital pressure.
The bottom line
The current cyber threat picture in the United States is clear. Active exploitation is constant. Nation-state campaigns are persistent. Critical infrastructure is a live target. Industrial systems are in scope. In that environment, zero trust is not an optional modernization language. It is a practical response to the fact that trust must now be earned, verified, limited, and continuously reassessed across the entire mission environment.
Chapter 9 | Federal health and biomedical missions run on resilient clinical IT
Federal health missions depend on far more than patient records
Federal health and biomedical missions are often discussed in human terms, and they should be. They involve patients, clinicians, researchers, public health leaders, laboratories, and care delivery teams. But none of those functions operate at scale without a resilient digital foundation. NIH says its Center for Information Technology provides the NIH community with secure and reliable IT infrastructure and scientific computing services that support mission-critical research and administrative activity, including enterprise networking, high-performance scientific computing, secure access to systems, data processing, hosting, storage facilities, cloud infrastructure, advanced algorithms, and data visualization.
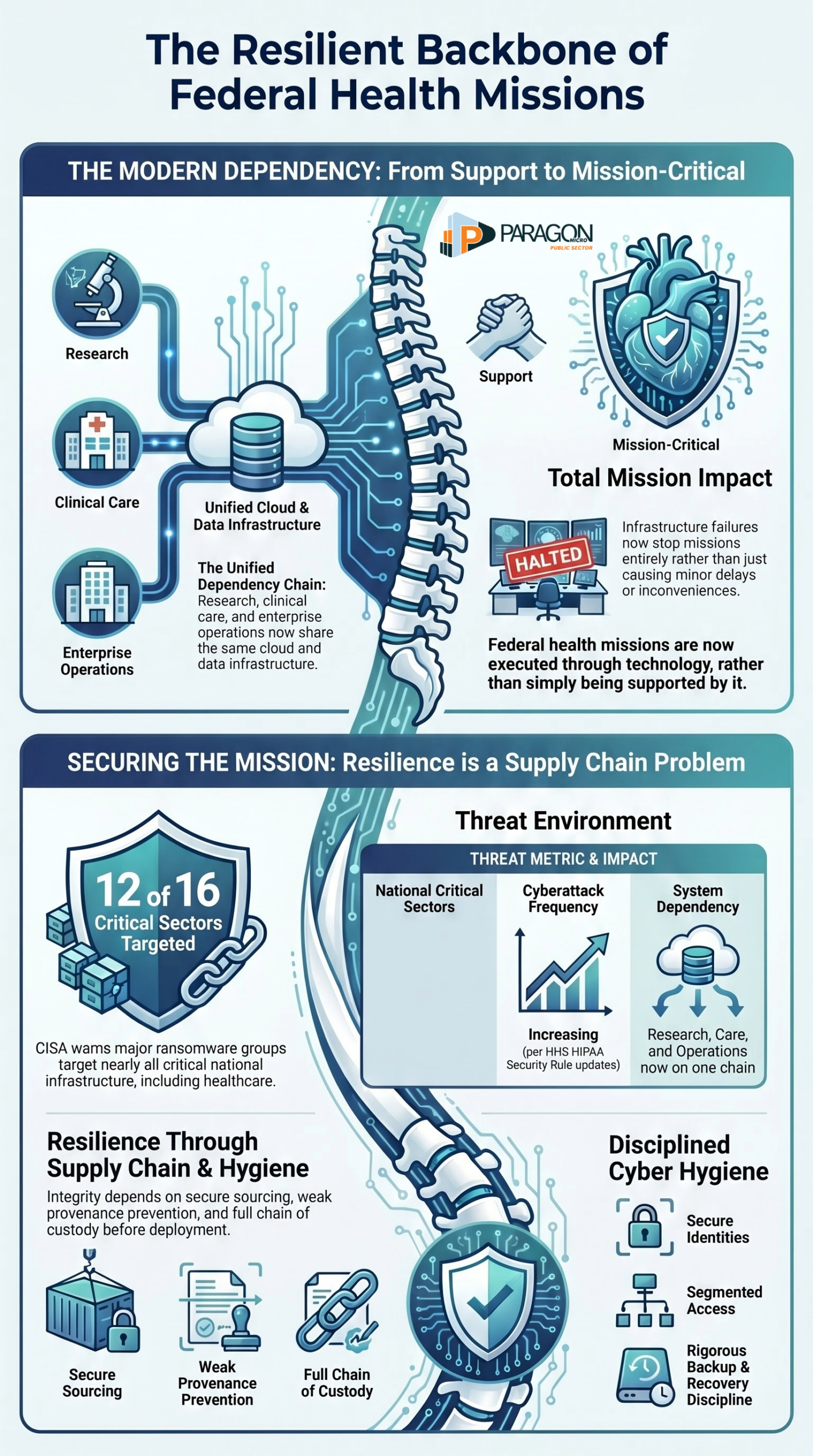
Clinical IT is now part of mission assurance
That matters because federal health missions are no longer supported by technology at the margins. They are executed through it. Biomedical research depends on computing and storage. Clinical operations depend on secure access and system availability. Public health coordination depends on data flow, interoperability, and trusted communications. NIH’s own description of CIT makes this clear by tying scientific computing, secure access, storage, hosting, and cloud directly to mission-critical activity.
Research, care, and operations now share the same dependency chain
The old mental model treated research IT, clinical IT, and enterprise IT as separate worlds. That separation is harder to defend now. NIH’s cloud and data science resources show that researchers increasingly rely on cloud storage, advanced computational infrastructure, and shared data environments to do their work. NIH’s STRIDES initiative materials likewise describe access to industry-leading cloud providers as a way to advance biomedical research. In practical terms, science, analytics, collaboration, infrastructure, and secure access now live on the same operational chain.
If the infrastructure fails, the mission does not simply slow down
In federal health environments, technology failures are rarely contained inconveniences. A storage issue can disrupt access to research. A network problem can delay coordination. An access control failure can interrupt clinical workflows. A cloud or hosting outage can impair continuity across multiple teams at once. HHS’s recent HIPAA Security Rule proposed updates explicitly state that they are responding to more frequent cyberattacks targeting the U.S. healthcare system, reflecting the seriousness of the operational risk.
The cyber threat against health systems is active and persistent
The healthcare and public health sector is not dealing with abstract cyber risk. HHS has published sector-specific cybersecurity performance goals to help healthcare organizations mature their defenses against expanding attack vectors, and ASPR TRACIE highlights those goals as part of sector resilience planning. CISA has also warned that major ransomware groups have targeted at least 12 of the 16 critical infrastructure sectors, underscoring that healthcare operates in a broader national threat environment rather than in isolation.
Healthcare resilience now requires disciplined cyber hygiene
HHS’s healthcare cybersecurity guidance emphasizes baseline and enhanced practices for the sector, including supplier cybersecurity requirements, which is a strong signal that resilience now depends on more than endpoint security alone. The point is bigger than compliance. Health missions depend on secure identities, segmented access, backup and recovery discipline, vendor risk management, protected data flows, and environments designed to keep functioning under pressure.
This is where federal health becomes a supply chain problem
Federal health systems are especially exposed because they depend on a wide mix of infrastructure, devices, software, networks, cloud services, storage, and external suppliers. That means resilience is not only a cyber issue or an uptime issue. It is also a sourcing, integration, and delivery issue. If systems arrive with weak provenance, poor configuration, or fragmented accountability, the mission inherits risk before clinicians, researchers, or administrators ever touch the technology. This is an inference drawn from the combined emphasis HHS places on supplier security and NIH places on mission-critical infrastructure dependence.
Paragon Micro’s health positioning fits this reality
Paragon Micro’s Federal Health Systems & Clinical IT solution is compelling in this context because it aligns to the actual dependency map federal health leaders are facing. The challenge is not simply buying more hardware or layering on another security tool. It is building secure, resilient, interoperable environments that support clinical continuity, research infrastructure, and protected operations at same time. When paired with Paragon Micro’s secure facility model, controlled integration, and full chain of custody approach, the value proposition becomes clearer: reduce preventable risk before these systems are deployed into environments where uptime, trust, and discretion matter.
The bottom line
Federal health and biomedical missions now run on resilient clinical IT, whether institutions frame it that way or not. Research, care coordination, public health, and operational continuity all depend on secure infrastructure, trusted cloud and storage, reliable access, and disciplined cyber resilience. In this environment, clinical IT is not a support infrastructure in the background. It is part of the mission itself.
Chapter 10 | Dependencies and interdependencies are now the battlefield
The real battlefield is not always where leaders think it is
Most organizations still imagine risk in straight lines. They picture a breach, a failed component, a delayed shipment, or an outage as a single event with a single cause. That is outdated thinking. The modern federal mission does not fail in straight lines. It fails through dependency chains. NIST warns that cyber supply chain risks are tied to decreased visibility into how technology is developed, integrated, and deployed, as well as the practices used to assure security, resilience, reliability, safety, integrity, and quality. That means the danger is not only the component you can see. It is the web of hidden relationships behind it.
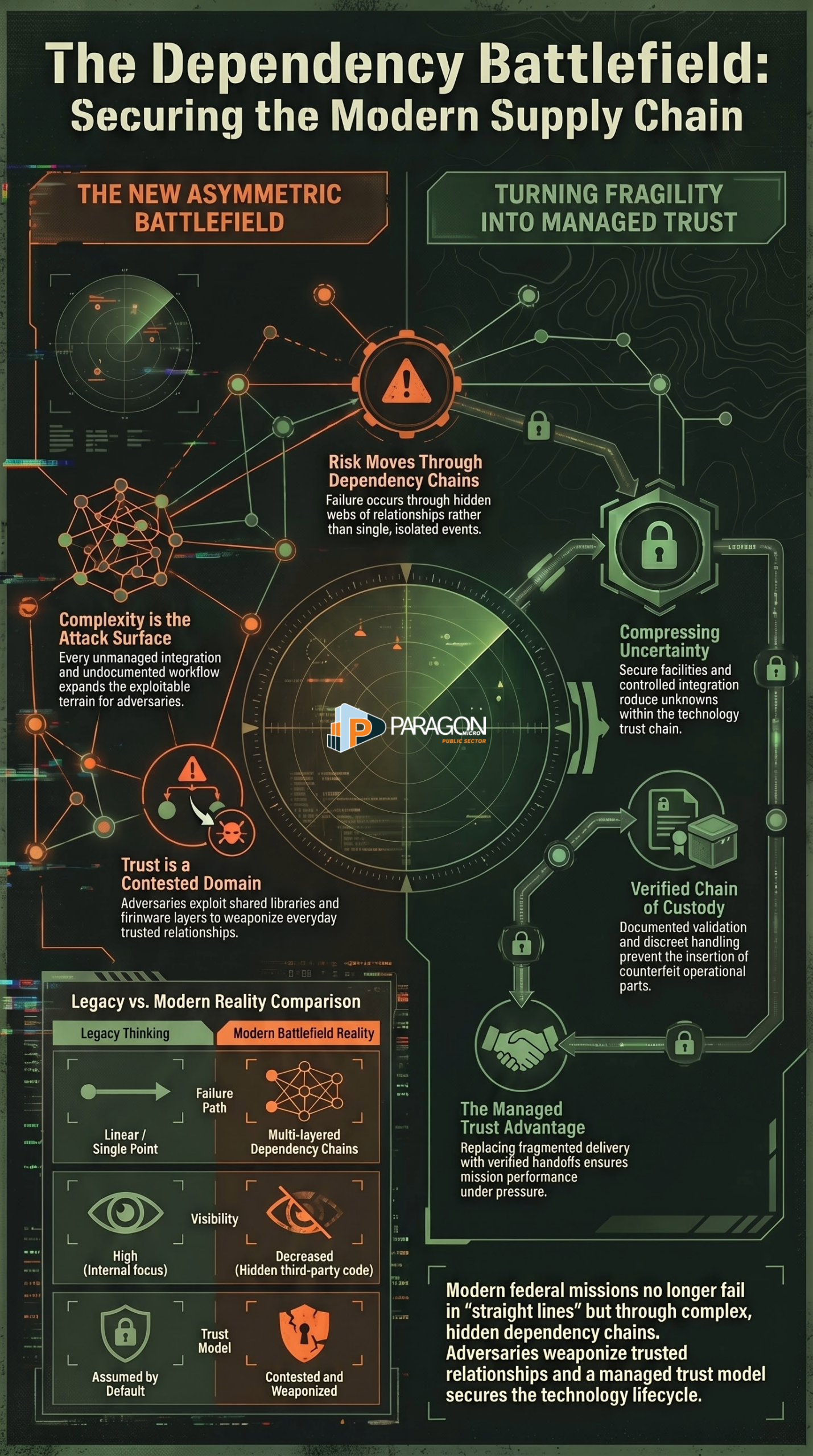
A single weak point can travel farther than expected
Interdependence is what makes modern systems powerful, but it is also what makes them fragile. CISA notes that a single connected component can introduce risk due to interdependencies among technologies and systems. That is the hard truth that many decision-makers still resist. One supplier issue can become a network issue. One software dependency can become an enterprise issue. One compromised component can become a mission assurance issue. The more connected the environment is, the farther one weak point can travel.
Adversaries do not need to break everything
This is what makes the problem asymmetric. A nation-state does not need to destroy an entire system to gain an advantage. It only needs to compromise a trusted relationship, a supplier, a dependency, a shared library, a firmware layer, or an integration point. The National Counterintelligence and Security Center says foreign adversaries abuse trusted supply chain relationships to advance campaigns and achieve effects. Its software supply chain guidance warns that adversaries exploit tools, dependencies, shared libraries, third-party code, and associated developer infrastructure. In other words, they attack the seams because that’s where trust is easiest to weaponize.
Complexity is now part of the attack surface
The deeper problem is that organizations often celebrate complexity as sophistication without acknowledging the cost. Every vendor handoff, every dependency, every unmanaged integration, every external code base, every undocumented workflow, and every unverified supplier expands the attack surface. NIST’s guidance exists precisely because federal agencies have less visibility, less understanding, and less control over how acquired technology is built, integrated, and delivered than many assume. Complexity is no longer just a management burden. It is exploitable terrain.
Trust is now a contested domain
That is the real shift. The contest is no longer only over networks, data, or endpoints. It is over trust itself. Can a component be trusted? Can a supplier be trusted? Can a software dependency be trusted? Can a delivered system be trusted? Can an operator trust that what arrived is what was ordered, that it was handled correctly, that it was not altered, and that it will perform under pressure? NCSC’s Deliver Uncompromised framework warns that adversaries can insert counterfeit parts that pass ordinary inspection but fail operationally, and that supply chain attacks can target the full lifecycle from conception to retirement. That makes trust a battlespace, not a buzzword.
Interdependence makes consequences compound
This is why interdependencies matter so much in federal missions. Research environments depend on compute, storage, networks, semiconductors, secure access, and software integrity at the same time. Health systems depend on clinical platforms, cloud, identity, and resilient infrastructure. C2 environments depend on visualization, networking, communications, edge devices, and uptime. When one layer weakens, the others do not stay untouched. They absorb the shock. CISA’s infrastructure assessments explicitly examine vulnerabilities, interdependencies, capability gaps, and the consequences of disruption because disruption rarely remains isolated.
This is why fragmented delivery is dangerous
A fragmented technology path creates blind spots. One vendor sources the part. Another stage it. Another integrates it. Another ship it. Another configures it in the field. Everyone touches the mission, but no one fully owns the trust chain. NIST’s supply chain risk guidance is really a warning about this exact condition: when visibility drops, risk rises. The mission then relies on assumptions rather than evidence. That is where preventable failure gets introduced long before deployment.
This is where Paragon Micro changes the equation
Paragon Micro’s value in this environment is not merely about delivering technology. It helps reduce the number of unknowns in the trust chain. A secure facility, controlled integration, documented validation, discreet handling, and full chain of custody matter because they compress uncertainty. They turn fragmented trust into managed trust. In a dependency-driven battlespace, that is a serious operational advantage. This is an inference based on federal supply chain risk guidance and Paragon Micro’s publicly described facility model.
The bottom line
Dependencies and interdependencies are no longer background conditions. They are the battlefield. The side that understands the chain, controls handoffs, verifies dependencies, and protects trusted relationships will operate with greater confidence and less surprise. The side that treats complexity as normal and trust as assumed will keep discovering risk too late, after the damage has already moved through the system.
Chapter 11 | The nation-state threat is already inside the problem set
Persistent threats are not random noise
The most dangerous misunderstanding in federal mission planning is treating cyber and supply chain threats like isolated incidents. They are not isolated. They are persistent campaigns. The 2026 Annual Threat Assessment states that cyber actors are targeting critical infrastructure to preposition for coercive or disruptive effects during a crisis, and it describes China as the most active and persistent cyber threat to the U.S. government, the private sector, and critical infrastructure networks. It also warns that Russia remains a persistent counterintelligence and cyberattack threat, with advanced capabilities and a history of compromising sensitive targets.
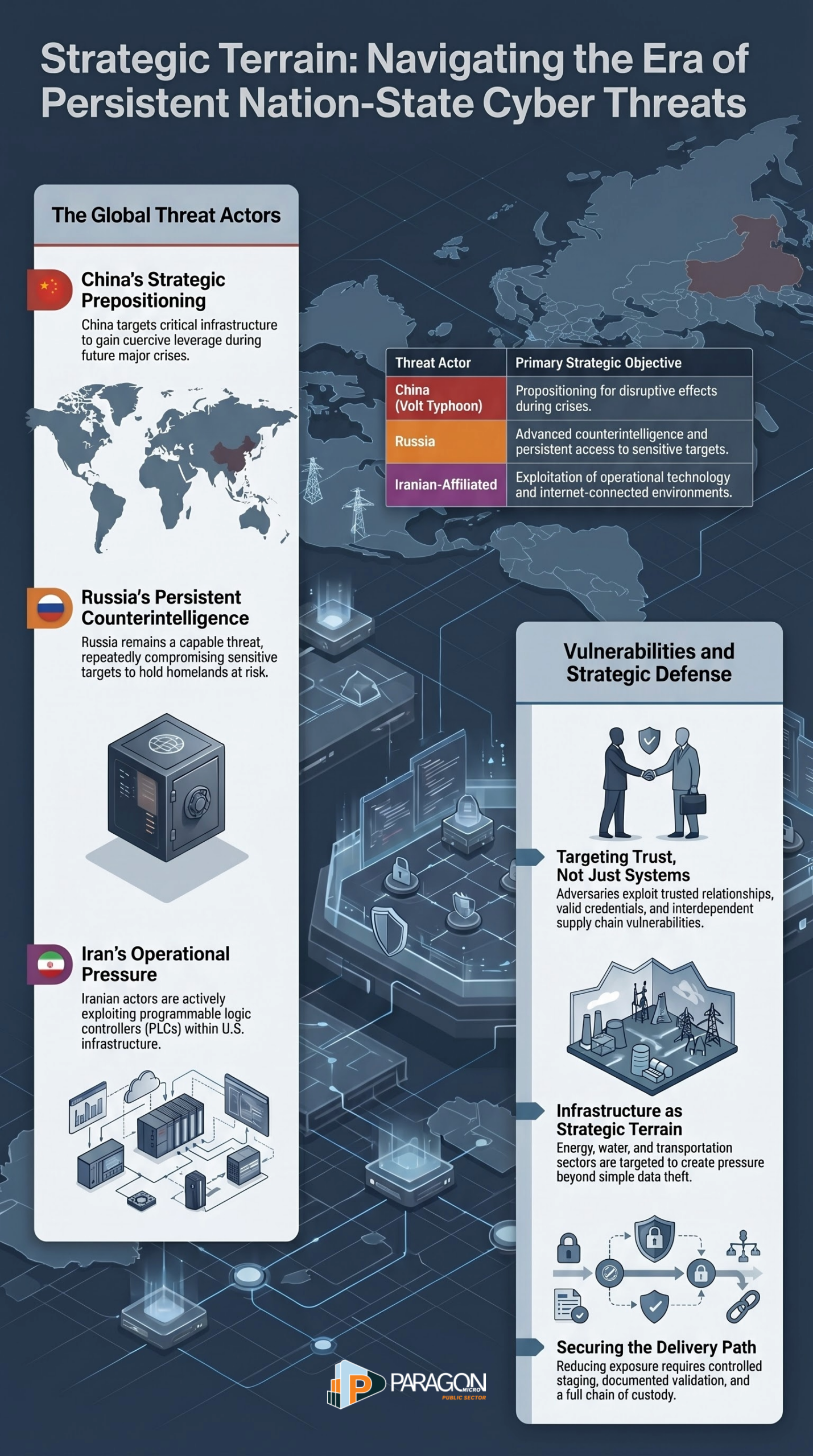
China is not probing for curiosity
The PRC threat matters because it is strategic, patient, and built for leverage. CISA, the FBI, the NSA, and partners have warned that Volt Typhoon compromised multiple U.S. critical infrastructure entities and maintained access, in part, to preposition for disruptive or destructive effects during major crises. That is not ordinary espionage. That is preparation. It means adversaries are not only trying to steal information. They are trying to shape future options by quietly embedding themselves where disruption would hurt most.
Russia remains a capable and persistent danger
Russia also remains a serious threat due to its advanced cyber capabilities and practical experience integrating cyber operations with broader national objectives. The 2025 and 2026 U.S. threat assessments both describe Russia as a persistent cyber and counterintelligence threat, including its repeated success in compromising sensitive targets and its willingness to hold the homeland at risk through cyber means. This is what persistence looks like in practice. The threat does not disappear because headlines shift. It stays in the environment, waiting for opportunity, access, or escalation.
Iran is showing how quickly cyber pressure can become operational pressure
Iranian-affiliated actors are also part of the current threat picture in a very direct way. On April 7, 2026, CISA published a joint advisory stating that Iranian-affiliated cyber actors exploited programmable logic controllers across U.S. critical infrastructure. CISA also maintains a broader Iran threat page warning of ongoing cyber exploitation targeting internet-connected and operational technology environments in the United States. This matters because PLCs are not abstract assets. They sit inside real-world systems. When adversaries target them, they are moving closer to operational consequences.
Persistence works because it targets trust, not just systems
What makes these threats so effective is that they do not need to crash everything at once. Persistent actors target trusted relationships, valid credentials, exposed edge devices, weak suppliers, software dependencies, and overlooked operational technology. They stay quiet when possible. They exploit patience. They let normal business processes carry risk deeper into the environment. CISA’s Volt Typhoon advisory and its Iran advisories both reflect the same lesson: the objective is often durable access, not flashy disruption on day one.
The country is absorbing a steady drumbeat of exploitation
This is happening against a backdrop of nonstop vulnerability exploitation. CISA’s Cybersecurity Advisories page and recent alerts show an ongoing cadence of newly exploited vulnerabilities and fresh threat advisories, including the April 2026 Iranian PLC warning and mid April 2026 additions to the Known Exploited Vulnerabilities Catalog. That cadence is important because it shows the country is not facing a single cyber season or a one-time wave. It is living inside a constant-pressure environment where adversaries keep testing for openings.
Critical infrastructure is part of the target set because it creates leverage
Nation-state actors target critical infrastructure because it gives them options beyond data theft. FBI and CISA statements have repeatedly emphasized that sectors supporting daily life are attractive precisely because disruption there creates pressure, fear, and strategic leverage. When adversaries preposition inside communications, energy, transportation, water, industrial control, or related systems, they are positioning themselves near the functions that keep society moving. That should change how agencies think about mission support technologies. They are no longer just business systems. They are strategic terrain.
Persistent threats exploit interdependence
This is where the supply chain and mission architecture issue becomes impossible to ignore. Persistent actors do not attack only the final target. They look for the easier path into it. That may be a trusted vendor, an exposed device, a remote management workflow, an upstream component, or an under-secured integration point. The more interdependent the system, the more routes there are to move from one weakness into a wider operational problem. This is an inference drawn from the current advisory pattern and the federal threat assessments.
This is why trusted delivery and controlled preparation matter
If persistent threats are patient, then agencies cannot afford to be casual about sourcing, integration, staging, or handoff. Systems that enter the mission poorly controlled, poorly documented, or sourced through fragmented channels create more uncertainty before deployment even begins. That is where Paragon Micro’s model becomes strategically relevant. A secure facility, controlled access, documented validation, discreet handling, and full chain of custody do not eliminate the threat from nation-states. They reduce preventable exposure and tighten the trust chain before systems enter high-consequence environments. This is an inference based on the documented threat environment and Paragon Micro’s publicly stated facility model.
The bottom line
Persistent threats are not future possibilities. They are the current operating conditions. China is persistent. Russia is persistent. Iranian-affiliated actors are active. Critical infrastructure is in scope. Operational technology is in scope. Quiet prepositioning is in scope. In that environment, agencies cannot focus solely on acquisition, modernization, or deployment speed. They have to think about endurance, trust, visibility, and control across the entire delivery path.
Chapter 12 | Counterfeits, gray market exposure, and lifecycle distortion
Gray market exposure is not a bargain; it is borrowed risk
Gray market sourcing looks attractive when programs are under pressure, parts are scarce, timelines are slipping, and official channels are slow. That is exactly why it is dangerous. The National Counterintelligence and Security Center says acquiring information and communications technology products or parts from independent distributors, brokers, and the gray market increases the risk of encountering substandard, subverted, and counterfeit products. It defines the gray market as the trade of parts through channels that are legal but unofficial, unauthorized, or unintended by the original component manufacturer. In other words, gray market exposure often begins as a convenience decision and ends as a trust problem.
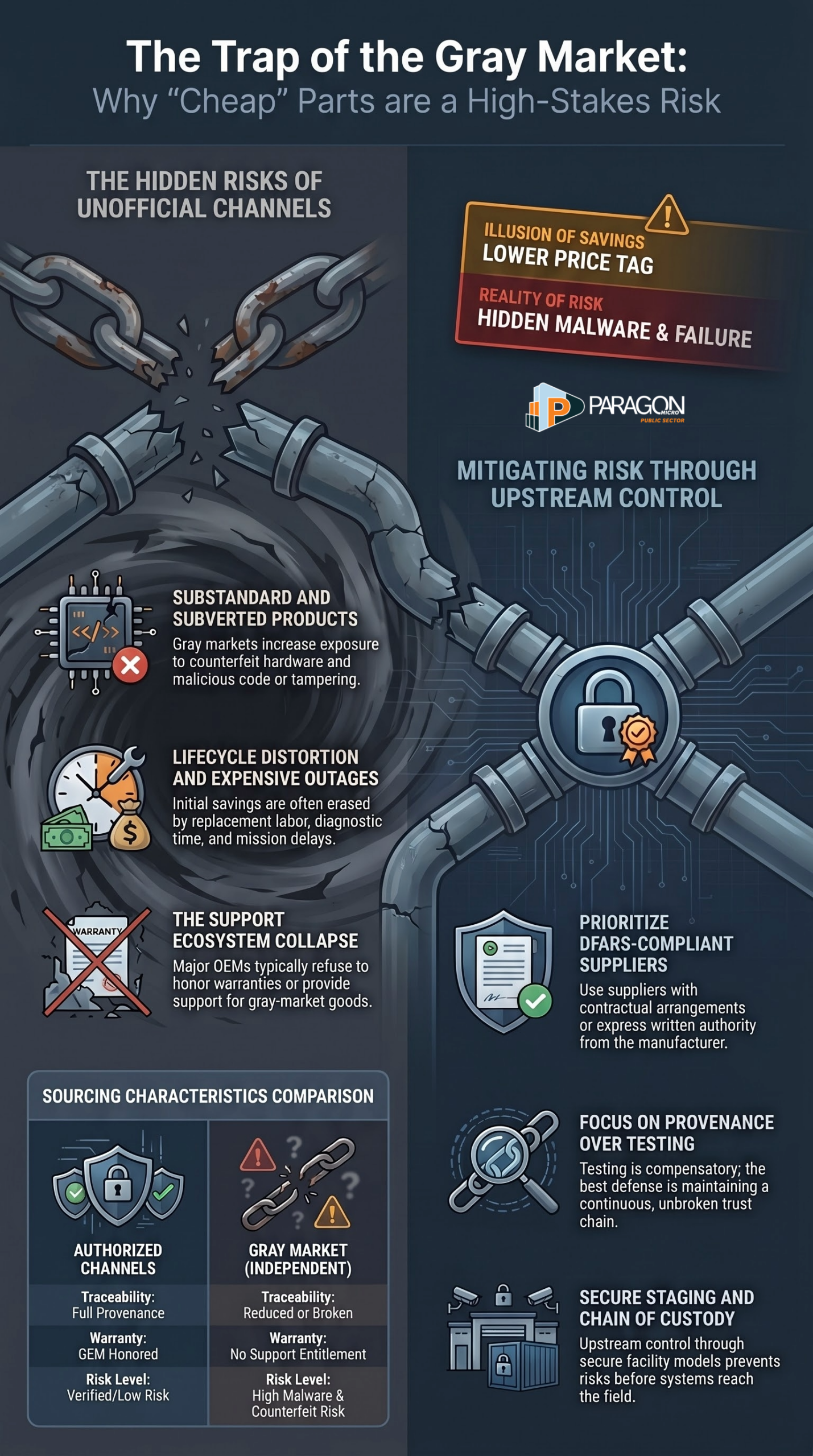
The real issue is not legality, it is loss of control
Many people hear “gray market” and assume the main question is whether the transaction is legal. That is the wrong question. The real question is whether the buyer still has confidence in the source, handling, integrity, and support. NCSC warns that products obtained through independent distributors and brokers leave devices vulnerable to counterfeit products and malicious code, while NIST warns that federal ICT supply chain risks stem from decreased visibility into how technology is developed, integrated, and deployed. Gray market exposure is therefore dangerous because it strips away the very controls that make assurance possible.
When visibility drops, counterfeit risk rises
NIST is blunt on this point. Federal agencies face risks from products and services that may contain malicious functionality, be counterfeit, or be vulnerable due to poor manufacturing and development practices, and those risks are exacerbated by decreased visibility into the supply chain. That matters because gray market channels almost always reduce traceability. Once traceability weakens, confidence in authenticity follows suit. The buyer may still receive a functioning part, but no longer has strong evidence that the part is genuine, unaltered, properly handled, or suitable for the intended mission.
Counterfeit parts do not always fail immediately
One of the most dangerous assumptions in procurement is that a part that powers on can be trusted. NIST’s supply chain threat scenario shows why that is naive. It describes counterfeit products that are visually identical to genuine ones, sold at a discount, purchased by unaware authorities, briefly tested, and then installed into systems where they may not fail for years. NIST notes that counterfeit elements can fail more often than expected, increase outages, reduce functionality, and impose significant operational and maintenance costs over time. The risk is not only instant failure. It is a delayed, distributed failure that erodes confidence and performance long after the purchasing decision is forgotten.
Cheap parts can become expensive outages
Gray market exposure distorts lifecycle economics. What looks like savings at acquisition often becomes a cascade of diagnostic time, replacement labor, operational disruption, and repeat maintenance. NIST’s counterfeit threat scenario describes exactly this pattern, showing how visually convincing counterfeit elements can enter storage, be installed during routine maintenance, fail later, and cause severe productivity losses and contract uptime violations. The low sticker price is often the least important number in the story.
Federal and defense systems are especially exposed
The Defense Department’s own oversight history shows how serious this problem is. GAO reported that the DoD supply chain is vulnerable to counterfeit parts, that those parts can delay missions and ultimately endanger service members, and that DoD draws from a large global network of suppliers and manages millions of parts across weapon and communication systems. GAO also found that multiple opportunities exist for counterfeit parts to enter systems during acquisition and sustainment because contractors rely on thousands of subcontractors and suppliers. Gray-market exposure is dangerous for any enterprise. In federal and defense environments, the consequences are magnified.
The internet and the broker market make the problem worse
This is not an edge case. GAO’s prior work found suspect counterfeit electronic parts available for purchase from companies selling military-grade parts online, and later reporting emphasized that a large number of such cases historically went unreported to the government or criminal authorities. Gray-market channels thrive in exactly that kind of environment, where urgency, scarcity, and fragmented oversight create openings for bad parts to move quickly.
Gray market exposure also creates malware and tampering risk
The problem is not limited to fake hardware. NCSC warns that insecure delivery and storage mechanisms leave devices vulnerable to the installation of hardware or software containing malware, and its broader supply chain guidance notes that adversaries can insert malware, hide foreign ownership, control, or influence ties, and counterfeit or manipulate key components and services. Once sourcing and custody become informal, the attack surface broadens from quality risk to adversarial manipulation risk.
Unauthorized channels often break warranty and support assumptions
Gray market exposure also distorts lifecycle support. Juniper states that when products are purchased through an unauthorized source, it cannot guarantee the source, quality, or security of gray-market products, and it does not honor warranties or support contracts for those products. Cisco likewise warns that products purchased from unauthorized resellers may have no Cisco warranty, may not be eligible for Cisco support, and may not carry a valid software license. This matters because support and warranty are not side benefits in mission environments. They are part of operational continuity.
No license, no warranty, no support means no real assurance
This is where gray-market exposure becomes a lifecycle distortion. The buyer may believe a product has been procured, but in practice, the organization may have acquired a device without valid support entitlement, without OEM warranty backing, without verified licensing, and without clean standing for future upgrades or maintenance. Cisco explicitly lists counterfeit products, diverted products, stolen products, counterfeit-upgraded products, gray, unauthorized products, and end-of-life or end-of-support products as risks associated with unauthorized markets. That means the hidden cost of gray-market buying is not just the risk of a bad unit. It is the collapse of the surrounding trust and support ecosystem.
Diverted and stolen goods are part of the gray market picture too
Another reason gray-market sourcing is so corrosive is that it blurs categories that should remain separate. Unauthorized markets can mix genuine but diverted products, stolen products, altered products, counterfeit upgrades, obsolete items, and outright fakes. Cisco’s own brand protection materials list each of those as distinct risks in the unauthorized market. Once products move outside authorized channels, the buyer may no longer know whether the box contains legitimate surplus, altered gear, stolen gear, cloned gear, or some combination of the above.
Disposal failures can feed the gray market
NIST highlights another overlooked angle: improper disposal. Its supply chain guidance specifically notes that proper disposal of information system components helps prevent those components from entering the gray market. This matters because not all gray-market exposure begins with a broker sourcing new-old stock. Some of it begins with retired or discarded components reappearing in unofficial channels, often with degraded reliability, incomplete provenance, or unauthorized rework. Gray market exposure is therefore not just a purchasing issue. It is also a lifecycle hygiene issue.
Obsolescence pressure is where bad decisions usually start
Programs often drift toward gray market channels when OEM production has ended, maintenance windows are closing, and replacements are hard to find. NIST’s counterfeit telecommunications scenario captures this precisely by identifying an element no longer produced by the OEM as a key vulnerability that allows counterfeit insertion into a trusted distribution chain. This is why obsolete systems are so operationally dangerous. Once the original channel dries up, urgency rises and trust standards often slip. That is where lifecycle distortion becomes visible. The system may still be in service, but the support model beneath it has already begun to decay.
Testing helps, but it does not restore provenance
Organizations sometimes assume that additional inspections can neutralize gray-market risk. Testing matters, but it is not the same thing as provenance. GAO notes DoD efforts to improve testing, traceability, and purchasing processes, and NIST recommends acceptance testing, serial and part number verification, digital imaging, digital signature verification, and sample electrical testing. Those are important controls. But even strong testing is compensatory. It exists because the original trust chain has already been broken. The better answer is usually to avoid creating the provenance problem in the first place.
Federal acquisition rules reflect this risk for a reason
Defense acquisition rules do not treat source discipline as optional. DFARS defines an authorized supplier as one with a contractual arrangement with, or the express written authority of, the original manufacturer or current design activity to buy, stock, repackage, sell, or distribute the part. The DFARS sources clause and related policy also make clear that when a contractor uses sources other than trusted or authorized suppliers, the burden shifts heavily toward inspection, testing, authentication, and traceability. The policy architecture itself reflects the reality that unofficial channels carry more risk.
Gray market exposure is really a trust chain failure
When you strip everything down, gray-market risk is not primarily about whether a part is cheaper, older, or harder to verify. It is about what happened to the trust chain. Who made it. Who was authorized to distribute it. Who handled it. Where was it stored? Was it altered? Was it diverted? Was it remarked? Was it repackaged? Was the firmware changed? Was malware introduced? Was the serial identity preserved? Can the OEM still support it. Each missing answer creates more uncertainty, and in mission environments, uncertainty is its own form of risk. This framing is supported by NIST’s emphasis on reduced visibility and by NCSC’s warning about substandard, subverted, and counterfeit products in gray-market channels.
This is why Paragon Micro’s model matters upstream
Paragon Micro’s value is not simply that it can deliver systems. It is that it can help reduce the conditions that allow gray market exposure to become a mission problem. Its facility model emphasizes controlled intake, secure staging, validation, documentation, and full chain of custody. In the context of gray market risk, that matters because the most effective mitigation is not heroic troubleshooting after deployment. It is upstream control before the system reaches the field. That is an inference based on NIST, NCSC, DFARS, OEM channel guidance, and Paragon Micro’s publicly described facility approach.
The bottom line
Gray market exposure is one of the most misunderstood risks in federal technology delivery. It weakens provenance, increases the risk of substandard, subverted, or counterfeit products, complicates support and licensing, raises the risk of malware and tampering, and distorts lifecycle economics by turning short-term savings into long-term mission drag. In high-consequence environments, unofficial sourcing is rarely just a procurement workaround. It is often the moment an organization trades control for uncertainty.
Chapter 13 | Software and firmware are now a supply chain terrain
Software is no longer just code; it is part of the mission pathway
Many organizations still talk about software risk as if it begins and ends with patching. That is far too narrow. Software now shapes how federal systems authenticate users, move data, coordinate workloads, manage devices, control updates, present operational pictures, and connect hardware to mission outcomes. Firmware does the same at a deeper layer by shaping how hardware behaves before most users ever see an interface. Once you understand that, the issue becomes obvious. Software and firmware are no longer supported. They are in the supply chain terrain.
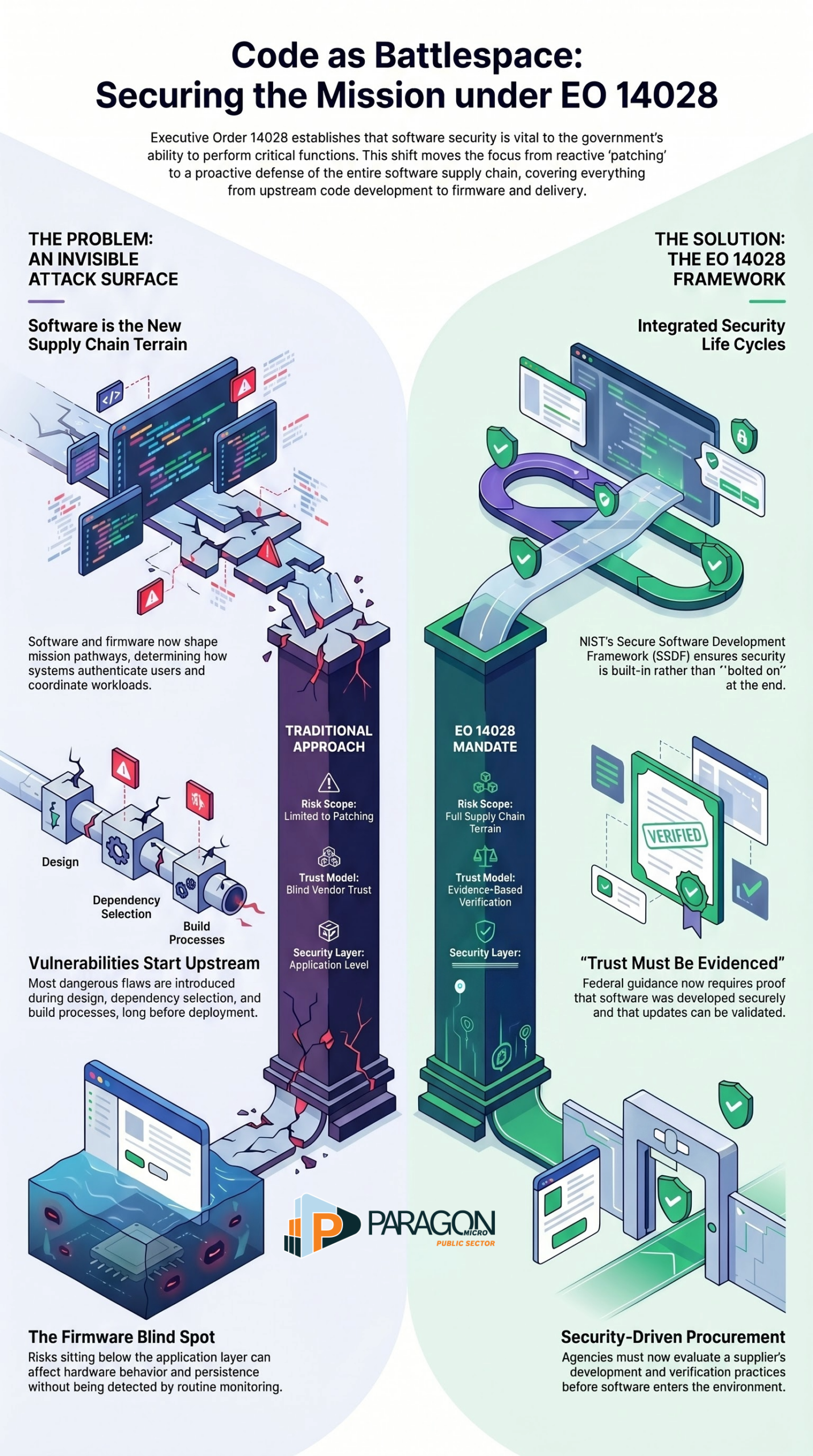
The federal government already says software security is mission-critical
NIST’s guidance under Executive Order 14028 states plainly that the security of software used by the federal government is vital to the government’s ability to perform its critical functions, and that there is a pressing need for more rigorous and predictable mechanisms to ensure products function securely and as intended. That is not a niche technical opinion. It is a direct statement that software assurance is now part of mission assurance.
Vulnerabilities are often introduced long before deployment
The most dangerous software problems do not start at the moment of exploitation. They start upstream during design, coding, dependency selection, build processes, packaging, signing, update handling, and deployment preparation. NIST’s Secure Software Development Framework exists because secure practices need to be integrated across the software development life cycle, not bolted on at the end. In other words, the vulnerability that appears in the field often began as a discipline failure much earlier in the chain.
Third-party dependencies quietly expand the attack surface
This is where the software supply chain becomes especially dangerous. Modern systems rarely consist of code written by a single team in a single place. They rely on third-party libraries, open-source packages, embedded components, vendor updates, firmware blobs, and external development infrastructure. NSA, CISA, and ODNI released joint guidance specifically because attackers are exploiting software dependencies, shared libraries, third-party code, and developer environments as practical attack paths. The more layers of inherited code a system depends on, the more places trust can break.
Firmware is often overlooked because it sits below visibility
Firmware risk is especially dangerous because it lives beneath the level many organizations routinely monitor. A system may appear healthy while running compromised, outdated, or poorly managed firmware that shapes device behavior at a foundational level. That makes firmware an attractive target in mission environments because it can affect reliability, persistence, hardware control, and recovery. When organizations focus only on applications and ignore lower layers, they leave one of the most consequential parts of the trust chain underexamined. This is an inference based on the role firmware plays in device function and the government’s broader software supply chain guidance.
Software compromise does not need to be loud to be damaging
One reason software supply chain attacks are so effective is that they can hide inside normal processes. Updates are expected. Dependencies are expected. Build automation is expected. Signed packages are expected. That makes compromise harder to spot because the adversary does not need to break in noisily. It can manipulate what the organization already trusts. CISA’s software supply chain materials focus heavily on prevention, mitigation, and resilience for exactly this reason. The attack often rides inside the legitimate workflow.
Secure development is now a procurement issue, too
This is not only a developer problem. It is also an acquisition problem. NIST’s software supply chain guidance was written in part to help federal agency staff know what information to request from software producers regarding secure software development practices. CISA’s software acquisition guide similarly helps buyers ask better questions about supplier practices. That is a major shift. Agencies are no longer expected to blindly trust software. They are expected to evaluate how it was built, protected, verified, and maintained before it is released into the environment.
Verification matters because trust must be evidenced
The federal response to software supply chain risk emphasizes verification for a reason. NIST’s EO 14028 materials cover software verification as a distinct workstream, and the SSDF emphasizes disciplined practices to reduce vulnerabilities and their impact. The larger message is simple. Trust is no longer a brand promise. It has to be backed by evidence that software was developed securely, that changes were controlled, that artifacts were protected, and that updates can be validated.
Attackers exploit the easiest path into trust
The asymmetry here is important. Adversaries do not need to compromise every system directly if they can compromise the software supply chain that feeds those systems. They can target developers, suppliers, build environments, dependency management, or update delivery. NSA, CISA, and ODNI’s joint releases for developers, suppliers, and customers all reflect the same lesson: software security is shared across the entire chain, and weakness at any point can undermine the whole.
Mission systems need secure software and controlled delivery together
This is where many organizations still think too narrowly. Even well-designed software can enter the field through a weak delivery path. Even strong hardware can be undermined by poor software discipline. That is why software assurance and physical chain of custody belong in the same conversation. If the mission depends on trusted systems, then the code, firmware, configuration, staging, validation, and delivery path must all support one another. This is an inference drawn from federal software supply chain guidance and broader supply chain risk management doctrine.
This is where Paragon Micro fits
Paragon Micro’s model matters here because software and firmware risk do not disappear when a box leaves the manufacturer. Systems still need controlled integration, configuration discipline, validation, documentation, and secure handling before deployment. In environments where mission owners care about trust, discretion, and readiness, upstream control over how systems are prepared becomes part of software supply chain defense, not separate from it. That is an inference based on Paragon Micro’s publicly described facility model and the government’s software supply chain guidance.
The bottom line
Software and firmware are now supply chain terrain because they shape how systems behave, what they trust, how they update, and whether they can be relied on under pressure. The federal government’s own guidance treats software security as vital to critical functions, emphasizes secure development across the life cycle, and warns that suppliers, developers, and customers all have a role in preventing compromise. In modern mission environments, code is not just part of the product. It is part of the battlespace.
Chapter 14 | Why fragmented sourcing and field assembly are operationally reckless
Fragmentation feels normal right up until it fails
Fragmented sourcing often looks efficient on paper. One vendor finds the hardware. Another handles staging. Another touches software. Another manages shipping. Another performs installation in the field. Another troubleshoots what the others assumed was already correct. It can look flexible. It can look fast. It can look cost-effective. In reality, it often creates a dangerous situation in which everyone participates in the mission, but no one fully controls the trust chain. NIST warns that cyber supply chain risk increases when organizations have decreased visibility into how technology is developed, integrated, and deployed, as well as into the practices used to assure security, resilience, reliability, safety, integrity, and quality. That is exactly what fragmentation produces: less visibility, more assumptions, and wider room for failure.
Every extra handoff creates another opportunity for uncertainty
The more times a system changes hands, the greater the opportunities for loss of provenance, configuration drift, improper storage, undocumented changes, packaging substitution, missed validation, or weak accountability. The danger is not merely theft or obvious tampering. It is the quiet accumulation of uncertainty. Who opened the box? Who updated the firmware? Who verified the serials? Who confirmed compatibility? Who validated the baseline? Who documented the change? In high-consequence environments, those are not administrative details. They are mission questions.
Field assembly is the worst place to discover what should have been controlled upstream
There is a hard truth here that many acquisition and operations teams learn too late. The field is the most expensive, least forgiving place to find out that a system was sourced poorly, configured inconsistently, incompletely documented, or never truly validated. Once equipment arrives in an operational environment, time compresses. Workarounds multiply. Technical debt becomes operational debt. Teams start improvising in the face of uncertainty because the mission still has to move forward.
That is why fragmented delivery is so dangerous. It shifts too much risk downstream into the exact environment least suited to absorb it. A system that should have been verified in a controlled facility is diagnosed in a command center, a clinical setting, a research environment, or at the tactical edge. By then, the cost of correction is higher, the margin for error is lower, and leadership is already exposed.
Fragmented sourcing breaks the evidence trail leaders need
NIST’s supply chain guidance is ultimately about evidence. It is about whether an organization can demonstrate how a system was built, sourced, handled, integrated, and prepared for use. Fragmented sourcing degrades that evidence trail. It replaces clean accountability with fragmented accountability. It turns controlled handling into partial visibility. It makes it harder to prove what happened and easier to assume what happened.
That matters because mission confidence is not built from optimism. It is built on traceability. If no one can clearly show where a system has been, who touched it, what changed, and how readiness was verified, then trust becomes a guess. In ordinary business environments, that may already be a serious weakness. In federal and high-consequence environments, it is operationally reckless.
Fragmentation creates friction that executives do not see until it is too late
One of the most deceptive aspects of fragmented sourcing is that early costs often remain hidden. The schedule may still appear on track. Parts may still arrive. Installation may still begin. But beneath that surface, friction grows. Teams spend more time reconciling mismatched versions, checking entitlements, confirming compatibility, chasing documentation, and resolving avoidable surprises. The mission feels slower, but the root cause is often disguised as ordinary complexity.
This is where the real asymmetry appears. Adversaries do not need to create all of that friction if the organization has already created it for them. A fragmented chain gives uncertainty more places to live. It gives weak controls more places to hide. It gives preventable failure more chances to move undetected into the operational environment.
Mission systems should not arrive as a puzzle
A mission system should never arrive as a loose collection of parts waiting for the field to figure it out. It should arrive controlled, validated, documented, and ready. That means we complete the integration, configuration, verification, and accountability work before deployment, not during it.
That is exactly why our model matters. Our System Readiness Center provides a secure, centralized environment for intake, staging, integration, validation, documentation, and delivery, with a full chain of custody. This matters because fragmented sourcing introduces too many unknowns across too many hands before the mission ever receives the system. We reduce those unknowns. We replace scattered trust with managed trust. We turn a loose chain of handoffs into a defined preparation path.
Controlled preparation is not a luxury; it is a risk reduction strategy
In high-consequence environments, centralized preparation is not about polish. It is about lowering the number of unresolved questions that reach the mission owner. Controlled integration means fewer configuration surprises. Documented validation means fewer assumptions. Secure handling means less exposure. A full chain of custody means stronger accountability. These are not cosmetic improvements. They are structural reductions in risk.
Paragon Micro’s facility messaging makes that case directly by emphasizing secure integration, controlled access, documentation, testing, validation, and chain of custody under one roof. In a world of persistent cyber threats, gray-market exposure, counterfeit risk, and dependency-chain fragility, that operating model is not just convenient. It is disciplined.
The real issue is not procurement efficiency; it is mission assurance
Too many organizations still evaluate sourcing models primarily through procurement logic: price, lead time, distributor availability, and installation speed. Those factors matter, but they are not enough. The real test is whether the sourcing and assembly model strengthens or weakens mission assurance. A fragmented approach may look cheaper or faster at the point of purchase, while quietly transferring uncertainty into integration, support, cyber exposure, and field performance.
That is the trap. Procurement efficiency without trust discipline is not efficiency. It is deferred risk.
The bottom line
Fragmented sourcing and field assembly are operationally reckless because they multiply handoffs, weaken traceability, push unresolved problems downstream, and force mission owners to absorb uncertainty at the highest consequence. The more sensitive the mission, the less acceptable that model becomes. Systems should be controlled before deployment, not explained after failure. That is why centralized integration, discreet handling, documented validation, and a full chain of custody matter. They are not process theater. They are how serious organizations reduce uncertainty before it becomes mission drag.
Chapter 15 | How Paragon Micro closes the trust gap
The value is not only what Paragon Micro delivers, but how it delivers it
By the time a federal system reaches a mission owner, most of the real risk has already been introduced or removed. That is the point many providers still miss. In this environment, value is not measured only by access to products, contract vehicles, or technical options. Value is measured by whether the delivery path strengthens trust or weakens it. Paragon Micro’s value proposition is compelling because it is built around that exact problem. Its System Readiness Center is positioned as a secure environment for integration, staging, testing, and delivery, where systems are engineered, validated, documented, and delivered with full chain of custody and, in its own words, “zero guesswork.”
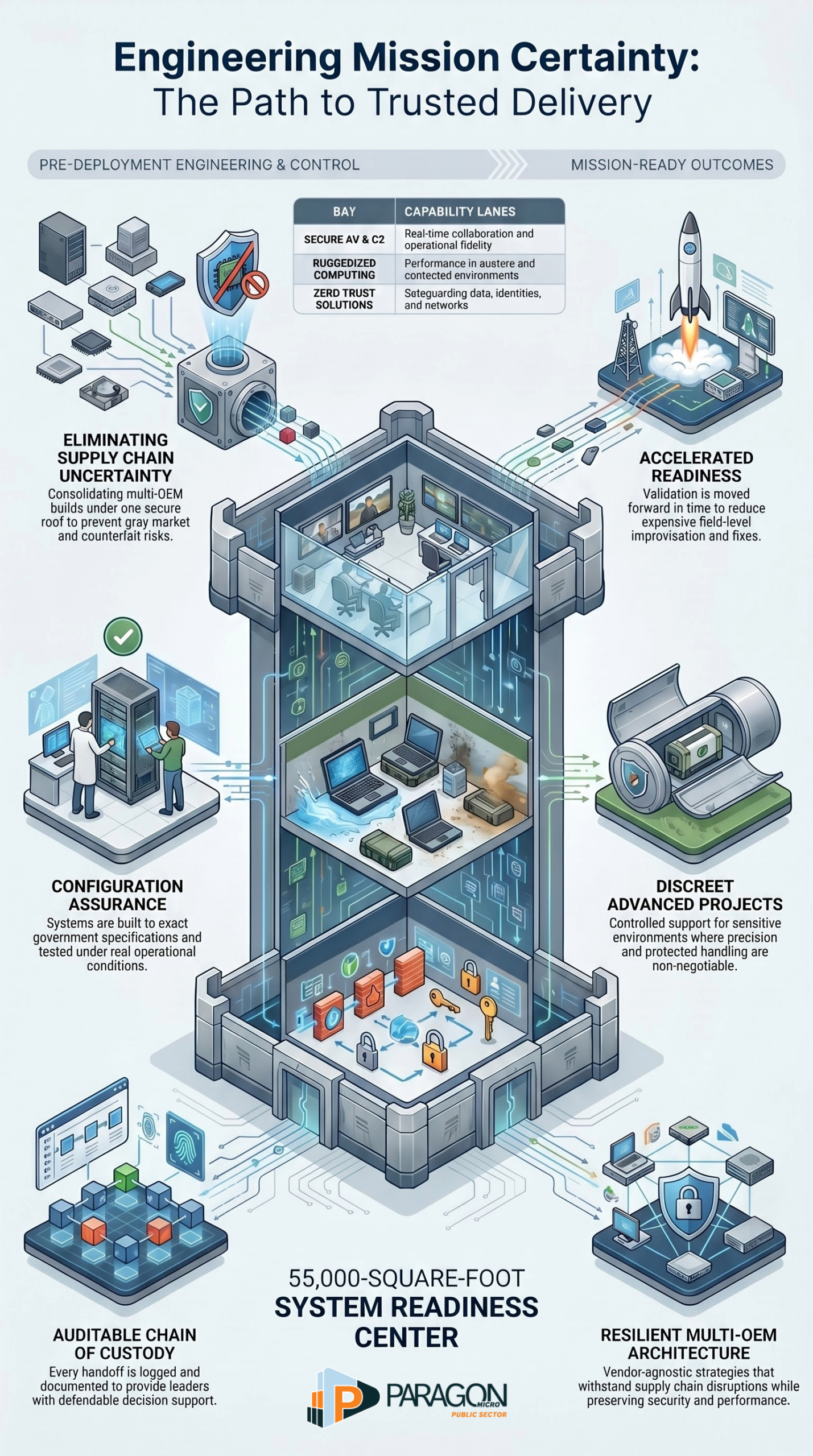
Paragon Micro turns product delivery into controlled mission preparation
That is the real difference. Many firms move boxes. Paragon Micro is trying to move certainty. Our System Readiness Center was built to bring design and architecture, modernization, system readiness, and lifecycle management together “to eliminate risk before deployment.” A 55,000-plus-square-foot secure integration facility where solutions are architected, configurations are validated, systems are staged and tested, and complete environments are prepared for delivery with documented precision. This shifts the conversation from fulfillment to mission preparation.
Control
Control is the foundation of our entire model. We built our facility around a simple reality: mission risk starts in the supply chain, not at deployment. Gray-market parts, counterfeits, unauthorized substitutions, tampering, and fragmented vendor staging all create visibility loss and national security risks. Our answer is to consolidate multi-OEM builds under one secure roof, verify every component, build to spec, and track every system from intake through delivery. That is a much stronger story than simple sourcing. We are not just acquiring technology. We are controlling the conditions around that technology before it enters the mission.
Configuration assurance
A large share of operational risk has nothing to do with whether a system can power on. It comes down to whether the system that arrived is the system intended. We address that directly. Every rack, system, endpoint, and component can be built to exact government specifications, integrated with mission-specific configurations, tested under real operational conditions, and documented at every step. For us, configuration assurance means building systems exactly to mission requirements, not adjusting them in the field. That is a compelling value proposition because it addresses one of the most expensive realities in federal IT: field-level improvisation caused by upstream inconsistency.
Accountability, which can actually be defended
Many providers talk about trust in vague terms. We make it concrete through auditable custody and documented handling. Every system is logged and tracked. Every configuration step is documented. Every handoff is controlled and auditable. Every delivery is validated against requirements. Our customers know where their systems have been, who touched them, and how they were handled from build through final delivery. In high-consequence environments, that is not marketing decoration. It is decision support for leaders who may later need to defend sourcing, integration, and readiness.
Faster readiness with fewer surprises
Our model is also operationally attractive because it moves validation forward in time. We speed deployment by building, testing, and validating systems up front so they arrive mission-ready, rather than waiting for field fixes. We also give customers the ability to see systems fully integrated before deployment, validate configurations, test performance and interoperability, and reduce downstream deployment risk. That matters because speed without validation is just accelerated uncertainty. Our approach is more credible because we tie faster deployment to predeployment assurance, not to shortcuts.
Discretion for sensitive environments
Some programs do not only need speed and accuracy. They need quiet precision. That is where the Advanced Projects positioning becomes important. That page leads with “Prepared discreetly. Delivered with precision.” It describes systems being received, staged, configured, validated, and prepared for deployment within a controlled environment that preserves accountability at every step.
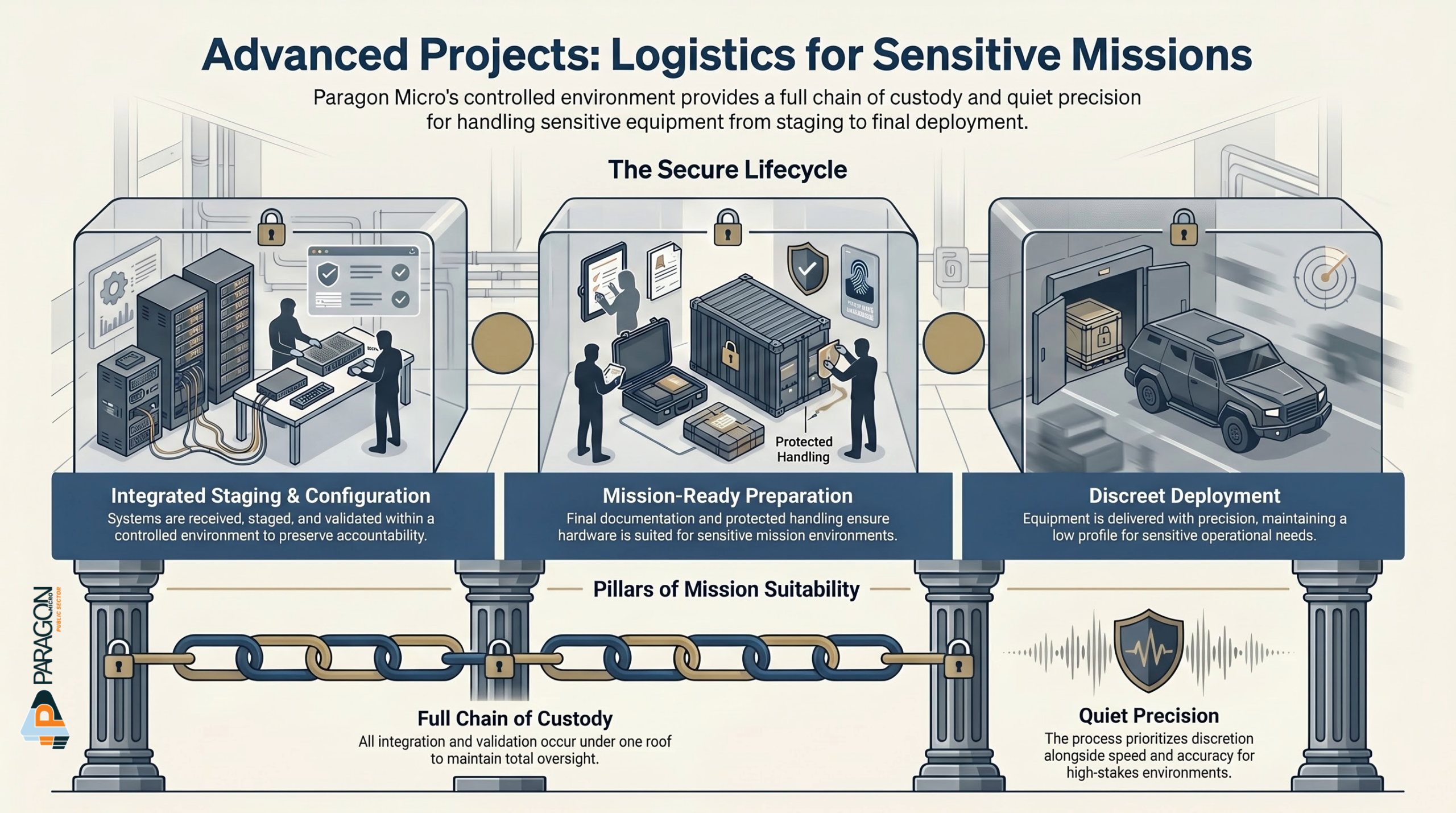
Paragon Micro provides controlled support where sensitivity, accountability, and precision matter from day one, with integration, validation, documentation, protected handling, and full chain of custody under one roof. That expands the value proposition beyond operational readiness and into sensitive mission suitability.
Flexibility without chaos
A common trap in government technology delivery is treating standardization like rigidity. We avoid that mistake by using a vendor-agnostic model built around mission requirements instead of forcing every need through a single OEM path. Our Advanced Projects work supports sensitive missions that rarely fit inside a rigid technology stack, so we align each solution to actual mission demands, security constraints, performance requirements, and deployment realities. We strengthen that approach through a resilient multi-OEM architecture that gives customers interoperable primary, secondary, and tertiary vendor strategies that can absorb supply chain disruptions while preserving security, continuity, performance, and acquisition flexibility. That value proposition stands out because it gives customers flexibility without sacrificing control.
Mission-aligned capability lanes
We strengthen our value proposition by tying our facility model directly to specific operational solution lanes. On our solutions page, we organize our capabilities around five core areas: secure AV and C2 environments that support real time collaboration and operational fidelity, ruggedized computing and communications built for austere and contested environments, multi OEM architectures that strengthen supply chain resilience, health and clinical IT that supports care continuity and data integrity, and zero trust solutions that protect data, identities, and networks while sustaining operational continuity in contested digital environments. That matters because our facility is not a generic warehouse. It is the enabling environment behind a mission-specific portfolio.
Lifecycle ownership, not one-time delivery
Another strong aspect of our model is that we do not treat our facility as a one-time staging point. We tie the environment directly to design and architecture, modernization, system readiness, and lifecycle management. Our lifecycle support includes ongoing sustainment, optimization, documentation, and upgrade planning to extend value and reliability over time. That adds more executive depth to our value proposition. It tells buyers we are not just focused on the initial transaction. We are focused on owning performance across the operational life of the system.
Reduced uncertainty
All of these elements create one larger benefit: uncertainty compression. That is the principle driving our model, even if we do not always label it that way. A secure facility reduces sourcing uncertainty. Documented validation reduces configuration uncertainty. Controlled handoffs reduce custody uncertainty. Up front testing reduces deployment uncertainty. Vendor-agnostic architectures reduce single-supplier uncertainty. Discreet handling reduces exposure uncertainty. Solution alignment reduces mission fit uncertainty. What we are really delivering is fewer unknowns crossing into the mission environment.
This is why the model matters in today’s threat environment
That is also why our value proposition carries more weight now than it would have a few years ago. In a climate shaped by persistent cyber threats, supply chain risks, gray market exposure, counterfeit concerns, and operational pressure to deploy faster, organizations need more than access to equipment. They need greater confidence in how equipment is sourced, integrated, handled, and delivered. Our model matters because we treat trust, accountability, and readiness as engineered outcomes rather than assumptions. That makes us easier to understand as a mission assurance partner, not just a reseller.
The bottom line
We close the trust gap by turning a fragmented technology-delivery problem into a controlled mission-readiness process. Our value proposition is not just secure products or even strong solutions. It is disciplined preparation. It is a validated integration. It is auditable custody. It is discreet handling. It is flexible sourcing aligned to mission needs. It is a faster deployment with fewer surprises. In high-consequence environments, that combination is worth far more than a lower price on a box.
Summary
For years, many organizations treated technology delivery like a procurement exercise. Buy the hardware. Move the boxes. Install the system. Hope the mission works. That model no longer fits the world we operate in.
Today, the mission depends on an enabling stack that starts long before deployment. Compute, semiconductors, software, communications, identity, cyber resilience, and supply chain integrity now shape whether federal missions can move with confidence or stall under pressure. The threat is no longer limited to a visible attack on a finished system. It lives upstream in compromised trust, weak provenance, fragmented sourcing, software dependencies, gray-market exposure, counterfeit risk, and quiet uncertainty that enter the environment before anyone in the field ever sees the equipment.
That is the real shift. The battlefield is no longer only the network. It is the chain of dependencies beneath the mission. It is the handoff. It is the supplier. It is the firmware. It is the staging process. It is the undocumented change. It is every place where trust is assumed instead of verified.
This is why the old belief that the mission begins when equipment arrives on site is obsolete. The mission begins much earlier. It begins when systems are sourced. It begins when they are integrated. It begins when they are validated. It begins when accountability is either built into the process or lost across too many hands.
That is also why our model matters. We do not treat trust as a slogan or readiness as a guess. We treat them as engineered outcomes. Through our System Readiness Center, controlled integration, documented validation, discreet handling, and full chain of custody, we reduce uncertainty before it reaches the mission. We do not just move technology. We prepare systems for consequence.
The deeper question every agency, mission owner, and federal buyer now has to confront is simple: Are you buying equipment, or are you buying confidence in what that equipment is, where it came from, how it was handled, and whether it is truly ready?
In a world defined by persistent cyber threats, supply chain pressure, contested environments, and shrinking margins for error, that question is no longer philosophical. It is operational. And the organizations that answer it well will hold an advantage long before the mission ever begins.
Take Control of Your Architecture Before It Controls You
When the mission is sensitive, the delivery path matters just as much as the technology itself.
Talk with Paragon Micro about how our System Readiness Center, controlled integration process, and full chain of custody help reduce risk before systems ever reach the field.
Research Methodology
This article uses a structured research methodology grounded in publicly available primary and authoritative sources. We reviewed federal strategy documents, threat assessments, standards, agency publications, acquisition guidance, and official cybersecurity advisories from organizations such as NIST, CISA, ODNI, NIH, DOE, GAO, HHS, and other U.S. government entities to identify the technologies, risks, and dependencies shaping federal mission performance. We then analyzed those sources for recurring themes, including technology dependence, supply chain fragility, cyber persistence, gray-market exposure, software assurance, and operational readiness. Finally, we mapped those findings against Paragon Micro’s publicly described facility, solutions, and delivery model to evaluate how secure integration, controlled validation, discreet handling, and full chain of custody address the specific trust and mission assurance gaps identified in the research.
References
- Boyens, J., Smith, A., Bartol, N., Winkler, K., Holbrook, A., & Fallon, M. (2024). Cybersecurity supply chain risk management practices for systems and organizations (NIST Special Publication 800 161r1 Update 1). National Institute of Standards and Technology. https://doi.org/10.6028/NIST.SP.800-161r1-upd1
- Cisco. (2022). Brand protection. Cisco Systems.
- Cybersecurity and Infrastructure Security Agency. (2024, February 7). PRC state sponsored actors compromise and maintain persistent access to U.S. critical infrastructure.
- Cybersecurity and Infrastructure Security Agency. (2026, April 7). Iranian affiliated cyber actors exploit programmable logic controllers across U.S. critical infrastructure.
- Cybersecurity and Infrastructure Security Agency. (2026). Cybersecurity advisories.
- Cybersecurity and Infrastructure Security Agency. (2026). Critical infrastructure assessments.
- Defense Advanced Research Projects Agency. (n.d.). Can I visit DARPA’s research labs?
- Defense Advanced Research Projects Agency. (n.d.). Offices.
- Federal Bureau of Investigation. (2024, April 18). Chinese government poses broad and unrelenting threat to U.S. critical infrastructure, FBI director says.
- Government Accountability Office. (2012). DOD supply chain: Suspect counterfeit electronic parts can be found on internet purchasing platforms (GAO 12 375).
- Government Accountability Office. (2016). Counterfeit parts: DOD needs to improve reporting and oversight to reduce supply chain risk (GAO 16 236).
- Intelligence Advanced Research Projects Activity. (n.d.). About IARPA.
- Intelligence Advanced Research Projects Activity. (n.d.). Our mission.
- International Maritime Organization. (n.d.). Red Sea project.
- Juniper Networks. (2020). Gray market product support FAQs.
- Juniper Networks. (2025). Gray market product reinstatement policy.
- National Center for Science and Engineering Statistics. (2025). Master government list of federally funded research and development centers. National Science Foundation.
- National Counterintelligence and Security Center. (2019). Deliver uncompromised: A strategy for supply chain security and resilience in response to the changing character of war.
- National Counterintelligence and Security Center. (2022). Protecting information and communications technology supply chains: Risks from adversarial exposure to the gray market and independent distributors. Office of the Director of National Intelligence.
- National Counterintelligence and Security Center. (2024). Protecting critical supply chains: Building a resilient ecosystem.
- National Counterintelligence and Security Center. (n.d.). Supply chain threats. Office of the Director of National Intelligence.
- National Institute of Standards and Technology. (2020). Zero trust architecture (NIST Special Publication 800 207). https://doi.org/10.6028/NIST.SP.800-207
- National Institute of Standards and Technology. (2022). Secure software development framework (SSDF) version 1.1 (NIST Special Publication 800 218). https://doi.org/10.6028/NIST.SP.800-218
- National Institute of Standards and Technology. (2022). Software supply chain security guidance under Executive Order 14028, section 4e. U.S. Department of Commerce.
- National Institute of Standards and Technology. (n.d.). Mission critical. NIST Computer Security Resource Center glossary.
- National Institute of Standards and Technology. (n.d.). Mission critical element. NIST Computer Security Resource Center glossary.
- National Institute of Standards and Technology. (n.d.). CHIPS for America.
- National Institute of Standards and Technology. (2023, September 19). National security. CHIPS for America.
- National Institutes of Health. (2025, June 12). Center for Information Technology (CIT). NIH Almanac.
- National Institutes of Health, Office of Data Science Strategy. (n.d.). STRIDES initiative.
- NSTC Fast Track Action Subcommittee on Critical and Emerging Technologies. (2024). 2024 critical and emerging technologies list update. Executive Office of the President.
- Office of the Director of National Intelligence. (2025). Annual threat assessment of the U.S. intelligence community.
- Office of the Director of National Intelligence. (2026). Annual threat assessment of the U.S. intelligence community.
- Paragon Micro. (n.d.). Advanced Projects.
- Paragon Micro. (n.d.). AV, C2 & Operational Workspaces.
- Paragon Micro. (n.d.). Facility.
- Paragon Micro. (n.d.). Federal Health Systems & Clinical IT.
- Paragon Micro. (n.d.). Resilient Multi OEM Architectures.
- Paragon Micro. (n.d.). Solutions.
- Paragon Micro. (n.d.). Tactical & Rugged Equipment.
- Paragon Micro. (n.d.). Zero Trust & Cyber Resilience.
- Reuters. (2026, April 11). U.S. military setting conditions to clear mines from Strait of Hormuz.
- Reuters. (2026, April 16). How the U.S. could clear mines from the Strait of Hormuz.
- Reuters. (2026, April 16). Oil prices rise on doubts U.S. Iran peace talks will ease Hormuz disruption.
- U.S. Department of Defense. (2022). Defense Federal Acquisition Regulation Supplement, Part 246, Quality assurance. Acquisition.gov.
- U.S. Department of Energy. (n.d.). National laboratories.
- U.S. Department of Energy, Office of Science. (n.d.). Office of Science national laboratories.
- U.S. Department of Health and Human Services. (2024). Cyber security guidance material.
- U.S. Department of Health and Human Services. (2024). HIPAA Security Rule notice of proposed rulemaking fact sheet.
- U.S. Department of Health and Human Services. (2024). HIPAA Security Rule NPRM.
- U.S. Department of Health and Human Services, Health Sector Cybersecurity Coordination Center. (n.d.). Healthcare and public health cybersecurity performance goals.
- U.S. Department of Justice. (2024, January 31). U.S. government disrupts botnet People’s Republic of China used to conceal hacking of critical infrastructure.
- U.S. National Security Agency, Cybersecurity and Infrastructure Security Agency, and Office of the Director of National Intelligence. (2022). Software supply chain guidance for developers.



