BLUF: You Do Not Lose Readiness on the Battlefield. You Lose It in the Contract and in the Architecture Diagram.
Adversary unmanned systems compress the timeline, widen the reconnaissance envelope, and make it harder for forces to hide, concentrate, communicate, and maneuver. Edge AI helps restore decision advantage by pushing detection, characterization, and decision support to the tactical edge.
The Department of Defense now drives a unified, Department-wide approach to countering unmanned systems, and it explicitly emphasizes detection, active and passive defenses, speed and scale, and institutionalization across Doctrine, Organization, Training, Materiel, Leadership and Education, Personnel, Facilities, and Policy (DOTMLPF‑P).
The DoW also warns that “non‑integrated, redundant solutions” slow the force down. Edge AI delivers value only when we integrate it into an open, modular C‑UAS architecture, sensing, AI-enabled decision support, and defeat: designed to operate when networks degrade.
Paragon Micro can help commanders and program teams turn “Edge AI” from a buzzword into a fieldable, governable, cyber-resilient capability that supports mission command under pressure, without breaking trust, safety, or compliance.
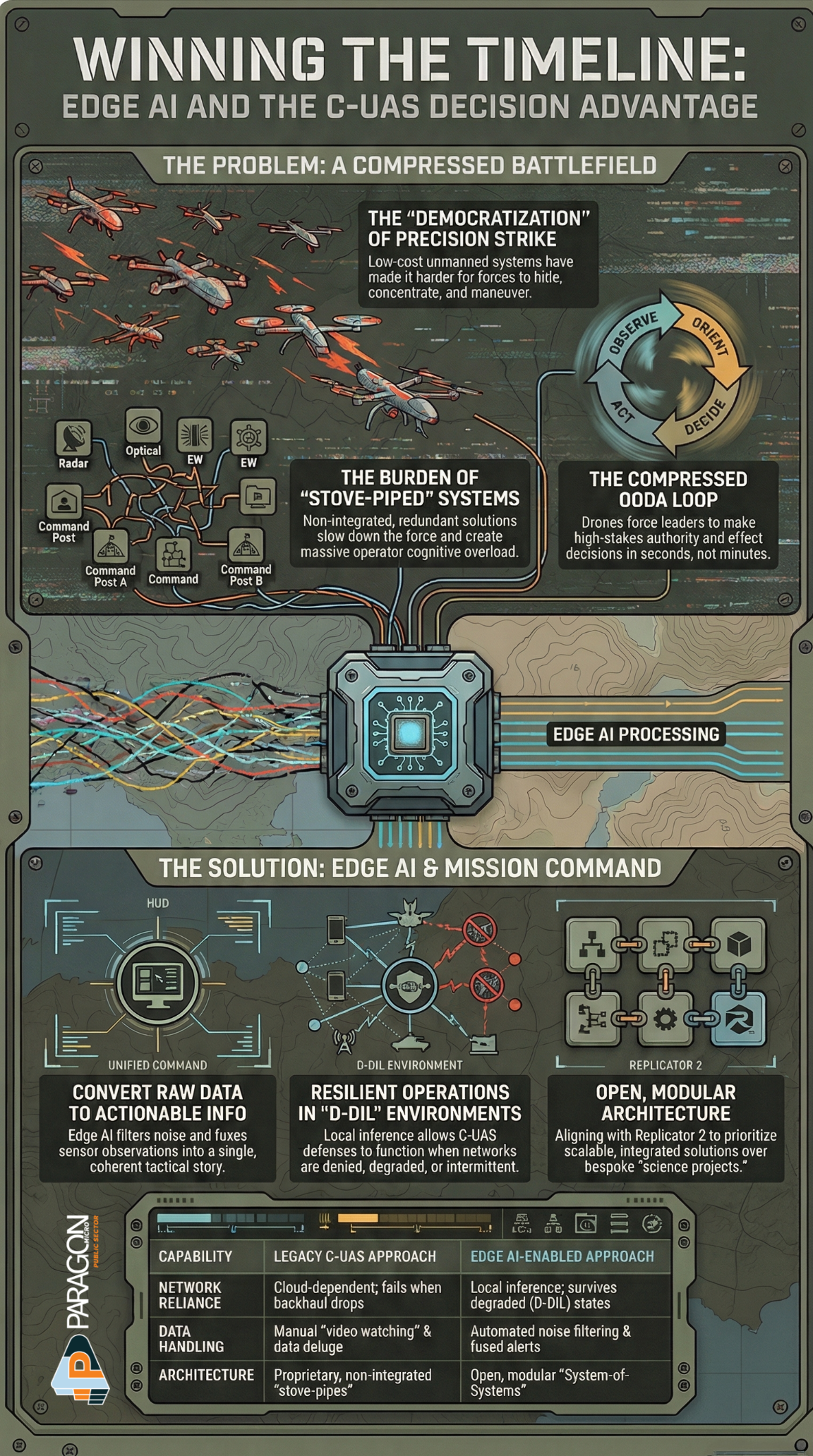
Table of contents
Chapter 1 — The battlefield already watches you
Chapter 2 — Reframe Counter‑UAS as a mission command problem
Chapter 3 — Edge AI as the shortest path to decision advantage
Chapter 4 — Build a C‑UAS “kill chain” that survives degraded networks
Chapter 5 — Design for speed and scale: open, modular, integrated
Chapter 6 — Trust the machine, but govern the machine
Chapter 7 — Secure the edge: treat every node as contested
Chapter 8 — Operationalize it: training, metrics, and experimentation
Chapter 9 — What Paragon Micro delivers
References
Chapter 1 — The battlefield already watches you
A formation no longer “enters contact.” It enters observation, often continuous, multi-sensor observation, before it hears the first shot. Modern doctrine recognizes this shift. Unmanned systems saturate the operating environment and contribute to persistent surveillance that challenges traditional concealment and movement.
The DoW now states this plainly: unmanned systems reshape tactics and compress innovation cycles, making it more difficult for forces to hide, concentrate, communicate, and maneuver. The same fact sheet warns that low-cost proliferation “democratized precision strike,” pushing risk down to the platoon, the convoy, and the perimeter.
Thought to carry forward:
If your unit treats drones as “a niche air defense problem,” it will lose time. If your unit treats drones as “an information problem that leads to a fires problem,” it will start winning the timeline.
Chapter 2 — Reframe Counter‑UAS as a mission command problem
Counter‑UAS does not start with the effector. It starts with command-and-control under uncertainty.
Army doctrine reminds us that decision-making demands the ability to act with imperfect information, and leaders must balance acting now with imperfect information with acting later with better information.
That doctrinal truth lands hard in the C‑UAS fight because small UAS compress the observe–orient–decide–act loop:
- Observe: Sensors see something fast, small, and ambiguous.
- Orient: Operators must decide whether the object matters, whether it threatens, and whether it belongs to us.
- Decide: Leaders must choose authorities, effects, and risk posture.
- Act: The unit must respond before the drone completes its mission.
Edge AI supports mission command when it helps commanders and crews make the right decision faster, not when it floods them with more data.
Chapter 3 — Edge AI as the shortest path to decision advantage
Edge AI does one thing exceptionally well when applied correctly: it converts raw sensor data into actionable information fast enough to matter.
That aligns with how the DoW frames the broader data fight. The DoW Data Strategy tells leaders to treat data as a weapon system and manage, secure, and use it for operational effect.
In practical C‑UAS terms, edge AI can:
- Filter noise at the source (reduce false alarms and operator overload).
- Fuse observations (turn “three sensors, three alerts” into “one track, one story”).
- Recommend actions (decision support that matches the commander’s intent and ROE constraints).
- Operate when comms degrade (local inference does not wait for a cloud round-trip).
Hard doctrinal question:
Do you want your C‑UAS team to “watch video,” or do you want them to command a defense?
Chapter 4 — Build a C‑UAS chain that survives degraded networks
The DoW emphasizes near-term improvement of defenses, with a focus on detection and active and passive defenses, while also preparing for more stressful future cases (including larger numbers of more capable, networked, and autonomous systems and swarms).
Edge AI contributes most when we design the system to survive “D‑DIL” realities (denied, degraded, intermittent, limited):
- Local sensing and local inference continue to work when the backhaul fails.
- Graceful degradation preserves mission-essential functions when a node drops.
- Mission orders for the machine define what it must do when humans cannot micromanage.
This is where doctrine and engineering meet. Mission command thrives when subordinates act in accordance with intent amid chaos. That same logic should govern edge autonomy: define boundaries, define authority, define reporting—and then let the system keep working when the network falters.
Chapter 5 — Design for speed and scale: open, modular, integrated
DoW strategy documents keep returning to one lesson: the Joint Force cannot afford bespoke, stove-piped counter‑UAS “science projects.”
The 2021 DoW Counter‑sUAS Strategy states that early approaches produced “many non-integrated, redundant solutions,” and it calls for a holistic, Department-wide approach.
The 2024 Strategy fact sheet drives this harder. It calls for delivery at speed and scale, prioritizes integrated, open, modular solutions, and explicitly highlights the need to reduce the cost imbalance between unmanned systems and countermeasures.
And Replicator 2 reinforces the same direction: DoW wants modular, mutually reinforcing solutions to sensing, AI-enabled decision support, and defeat, appropriate to the range of environments that host critical installations and force concentrations.
What this means for Edge AI:
Edge AI must plug into a system-of-systems architecture. It must not require units to replace everything else they already field.
Chapter 6 — Trust the machine, but govern the machine
If you want operators to trust AI in a lethal or safety-critical context, you must build governance into the system, not bolt it on later.
DoW guidance lists AI ethical principles (Responsible, Equitable, Traceable, Reliable, Governable) and applies them to DoW AI capabilities, including warfighting use cases.
In C‑UAS terms, governance looks like this:
- Traceability: The system logs why it classified a track and what data it used.
- Reliability: The system proves performance under realistic conditions (weather, clutter, novel targets).
- Governability: The unit can constrain, override, and shut down AI behaviors.
- Responsible use: Humans retain accountability for force decisions and authorities.
Thought-provoking truth:
If your AI cannot explain itself at the speed of combat, it will not earn trust, so it will not get used when it matters.
Chapter 7 — Secure the edge: treat every node as contested
Counter‑UAS does not just fight drones. It counters the adversary’s attempts to exploit your electromagnetic signature, networks, and seams.
The DoW Zero Trust Strategy frames zero trust as a strategic shift to secure and protect the DoW Information Enterprise and accelerate adoption through Department-wide coordination.
For edge AI in C‑UAS, that implies:
- Identity-first access for devices, models, and operators
- Signed and verified updates for models and containers
- Segmentation so that one compromised sensor node does not collapse the defense
- Secure logging and auditing to support investigations, safety, and learning
Chapter 8 — Operationalize it: training, metrics, and experimentation
DoW strategy calls for clear metrics and measures of effectiveness to track progress.
The fastest way to fail with edge AI is to measure the wrong thing.
C‑UAS edge AI must prove value in mission outcomes:
- Time-to-alert and time-to-characterize (not just “model accuracy”)
- Operator workload (alerts per hour; false alarms per shift)
- Track continuity in cluttered environments
- Interoperability across sensors, C2, and effectors
- Performance in degraded networks (how it behaves when comms drop)
The Army’s Joint Counter‑Small UAS Office has already run demanding demonstrations that stress command-and-control and sensing across multiple systems, launching more than 40 UAS targets per session and evaluating C2 performance across nine systems. That kind of operationally relevant testing is the right model.
Chapter 9 — What Paragon Micro delivers
Paragon Micro can help teams translate doctrine into deployed capability by focusing on integration, resilience, and governance, the exact problem areas DoW highlights.
1) System integration that avoids “redundant solutions.”
We integrate edge compute, sensors, and C2 interfaces into an architecture that reduces duplication and accelerates fielding, directly addressing DoW’s warning about non-integrated, redundant approaches.
2) Edge AI that supports mission command
We structure edge AI outputs around operational decisions—tracks, confidence, recommended actions, and audit trails so commanders act faster without demanding perfect information.
3) A path to speed and scale
Replicator 2 explicitly targets barriers in production capacity, open system architecture, system integration, policies, and authorities, and it expects improved protection within 24 months of funding approval. We build solutions that match that reality: modular, testable, and ready to plug into programs of record.
4) Responsible AI and cyber resilience at the edge
We embed governance (traceability, reliability, and human control) and security (zero-trust principles) into the architecture from day one.
Recommended “first engagement” package for a program office or unit
- Operational vignette workshop: define mission threads, authorities, and decision points
- Edge architecture sprint: map sensors → edge compute → C2 outputs; define degraded-mode behaviors
- Pilot demonstration: measure time-to-alert, false alarms, workload, and interoperability
- Governance plan: logging, model update controls, test thresholds, and operational constraints
Take Control of Your Architecture Before It Controls You
The threat is not waiting for perfect specifications.
And your adversary is not pausing while you evaluate options.
If Edge AI is going to matter in C-UAS operations, it must be integrated, resilient, governable, and field-ready under contested conditions.
Now is the time to move from concept to capability.
If your program depends on proprietary boundaries, unclear data rights, or undefined integration authority, now is the time to act.
Our federal team works with defense and civilian agencies to design modular, governable, rights-aware architectures that accelerate modernization without sacrificing accountability.
If you are planning a new acquisition, facing a sustainment bottleneck, or preparing for a major refresh, let’s have a focused conversation.
Engage the Paragon Micro Defense Team for a focused operational session. In one working discussion, we will:
- Map your current sensors, C2, and edge compute posture
- Identify latency, bandwidth, and integration gaps
- Define degraded mode behaviors and mission command constraints
- Establish measurable pilot criteria aligned to DoW strategy
- Deliver a clear path from architecture to field evaluation
We do not sell isolated components.
We deliver integrated, modular, mission-ready capability.
If you are responsible for protecting installations, maneuver forces, or critical infrastructure against unmanned threats, let us build the architecture that restores decision advantage at the edge.
Schedule your Counter UAS Edge AI architecture session with the Paragon Micro Defense Team today and turn architecture into a readiness advantage.
Win the timeline.
Control the architecture.
Protect the mission.
References
- Department of Defense. (2021). Department of Defense counter-small unmanned aircraft systems strategy.
- Department of Defense. (2024, September 30). Secretary of Defense memorandum: Replicator 2 direction and execution.
- Department of Defense. (2024, December 5). DoD announces strategy for countering unmanned systems (News release).
- Department of Defense. (2024, December 5). Fact sheet: Department of Defense strategy for countering unmanned systems.
- Defense Innovation Unit. (2024). The Replicator initiative (Replicator 2 overview).
- Headquarters, Department of the Army. (2019). ADP 6-0: Mission command—Command and control of Army forces.
- Headquarters, Department of the Army. (2022). FM 3-0: Operations.
- Office of the Secretary of Defense. (2020). DoD data strategy: Unleashing data to advance the national defense strategy.
- Office of the Secretary of Defense. (2022). DoD zero trust strategy.
- U.S. Department of Defense. (2021). Implementing responsible artificial intelligence in the Department of Defense (Memorandum).
- U.S. Department of Defense. (2024). Responsible artificial intelligence strategy and implementation pathway.
- U.S. Department of Defense. (2025, August 28). Establishment of Joint Interagency Task Force 401.
- U.S. Department of the Army. (2024, July 26). Joint Counter-Small UAS Office conducts successful counter drone-swarm demonstration.



