What We Deliver
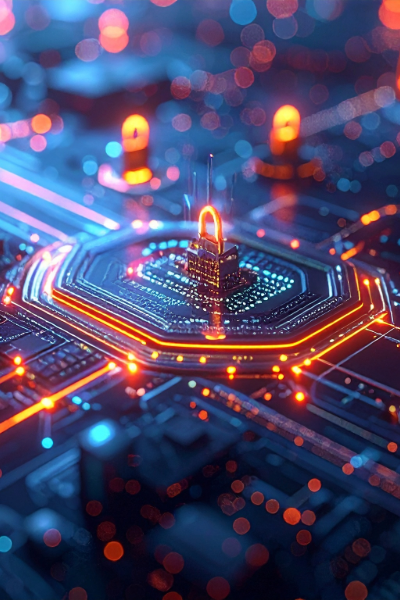
Zero Trust Architecture
We map users, devices, applications, data flows, and trust boundaries across on-prem, cloud, and tactical environments. Architectures are tailored to mission requirements, not generic frameworks.
Identity & Access Control
Strong identity becomes the new perimeter. We implement persistent multi-factor authentication, role-based access controls, device trust validation, and continuous authorization.
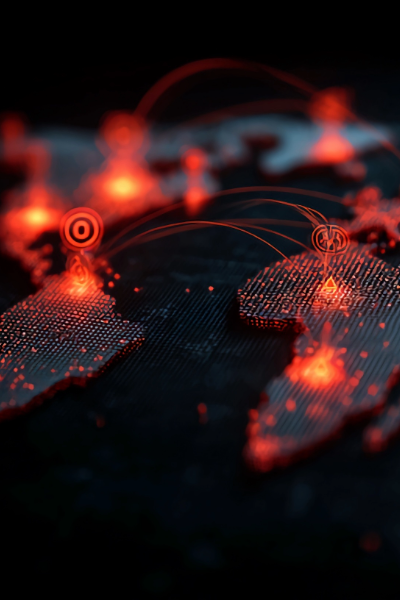
Network Segmentation
Microsegmentation limits malicious lateral movement and blast radius. Compromised systems are isolated before damage spreads across critical mission environments worldwide.
Secure Cloud & Hybrid Ops
Enterprise Zero Trust policies extend consistently across cloud, hybrid, and disconnected environments without breaking operations or disrupting mission critical workflows at scale.
Cyber Resilience
Security does not stop attacks. Resilience ensures the mission continues anyway. We design backup, failover, and recovery strategies that withstand ransomware, data corruption, and system outages.
Our Zero Trust & Cyber Resilience Solution
Modern cyber threats are persistent, adaptive, and often already inside the network. Zero Trust and cyber resilience are not security buzzwords. They are operational requirements. We help government and mission-critical organizations design, deploy, and sustain Zero Trust architectures that reduce attack surfaces, enforce continuous verification, and ensure operations continue even when systems are under attack.
BLUF: Modern cyber threats are persistent, adaptive, and often already inside the network. Zero Trust and cyber resilience are not security buzzwords. They are operational requirements. We help government and mission-critical organizations design, deploy, and sustain Zero Trust architectures that reduce attack surfaces, enforce continuous verification, and ensure operations continue even when systems are under attack.
Core Principles We Enforce
Powered by Trusted Technology Leaders
Why Zero Trust Alone Is Not Enough

Zero Trust reduces risk by limiting access and containing threats. Cyber resilience ensures operations continue when defenses are tested or breached.
We integrate both into a unified approach.
When breaches occur, resilient systems:
- maintain critical services under pressure.
- preserve data integrity and availability.
- enable rapid containment and recovery.
- prevent single points of failure across environments.
This is how organizations move beyond cyber defense and achieve true cyber survivability.


Who This Is For

This solution is designed for organizations where security failures, operational disruption, or loss of trust directly threaten mission success, including:
- Federal civilian agencies operating in regulated environments.
- Defense and intelligence programs with mission-critical systems.
- State and local governments delivering essential public services.
- Critical infrastructure operators protecting high-value assets.
- System integrators supporting compliance-driven environments.
If downtime, data loss, or unauthorized access threatens mission success or public trust, this solution applies.
Our Differentiator

Our differentiator is outcome-driven Zero Trust engineering, grounded in deep federal experience, mission risk awareness, acquisition realities, and disruption-free modernization, delivered through our role as a trusted Value Added Reseller providing end-to-end support.
Our team understands:
- regulated federal environments.
- mission and operational risk.
- acquisition constraints and compliance realities.
- legacy modernization without disruption.
Every Zero Trust deployment is designed, integrated, and supported end-to-end to serve real missions, real users, and real operational timelines.


The Result

This approach delivers measurable risk reduction, faster threat response, stronger identity control, and resilient operations that safeguard mission execution for federal, defense, and state and local government organizations, even under active attack.
This strategic solution ensures:
- reduced attack surface through continuous verification and segmentation.
- faster detection and containment of active threats.
- stronger identity-based security across users, devices, and systems.
- resilient systems that continue operating under attack or disruption.
- measurable improvement in cyber posture and overall mission assurance.
Past Performance
Paragon Micro strengthens federal environments with Zero Trust-aligned architectures and cyber-resilient infrastructure designed to withstand evolving threats.
Our past performance includes:
- Implementing identity-centric access controls and least privilege enforcement
- Segmenting networks to reduce lateral movement and contain compromise
- Integrating multi-factor authentication and secure endpoint validation
- Hardening data storage and transport with FIPS-aligned encryption standards
- Modernizing legacy environments to meet federal cybersecurity mandates
We baseline dependencies, validate configurations in staging, and deploy with controlled cutovers to protect mission continuity. The result is a hardened operational environment built to detect, resist, and recover from cyber threats without disrupting critical operations.
Discuss Your Mission Challenge
Connect with Paragon Micro to discuss securing what matters most.